Cloudflare MCP Server for Claude Code 25 tools — connect in under 2 minutes
Claude Code is Anthropic's agentic CLI for terminal-first development. Add Cloudflare as an MCP server in one command and Claude Code will discover every tool at runtime — ideal for automation pipelines, CI/CD integration, and headless workflows via the Vinkius.
ASK AI ABOUT THIS MCP SERVER
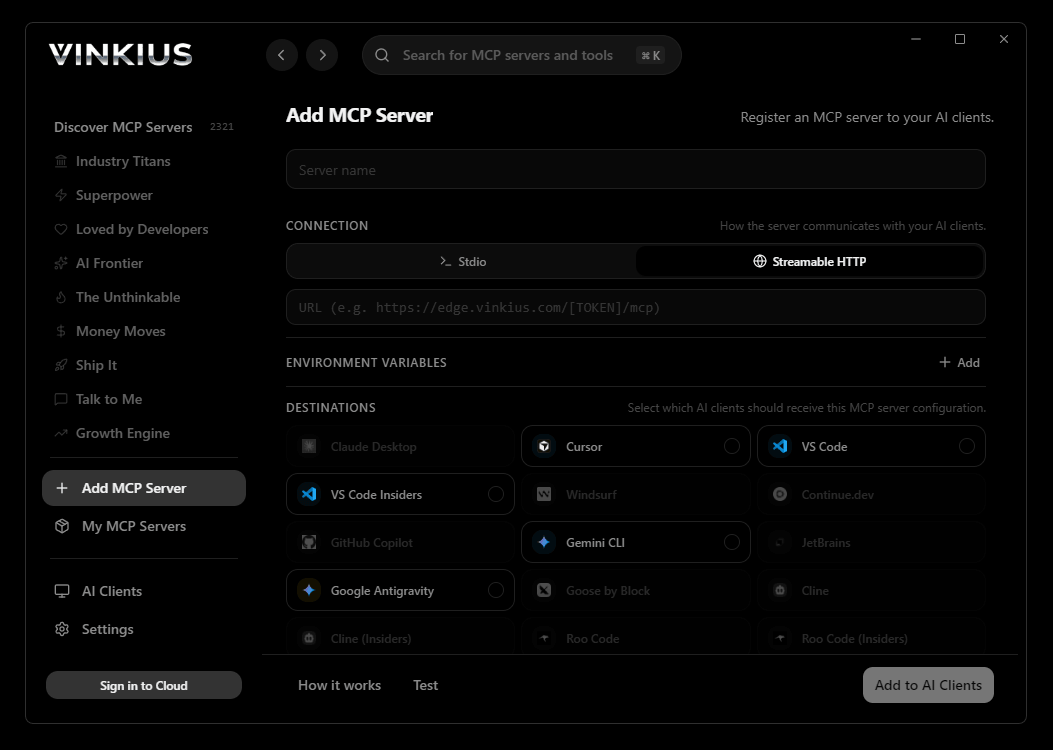
Vinkius supports streamable HTTP and SSE.
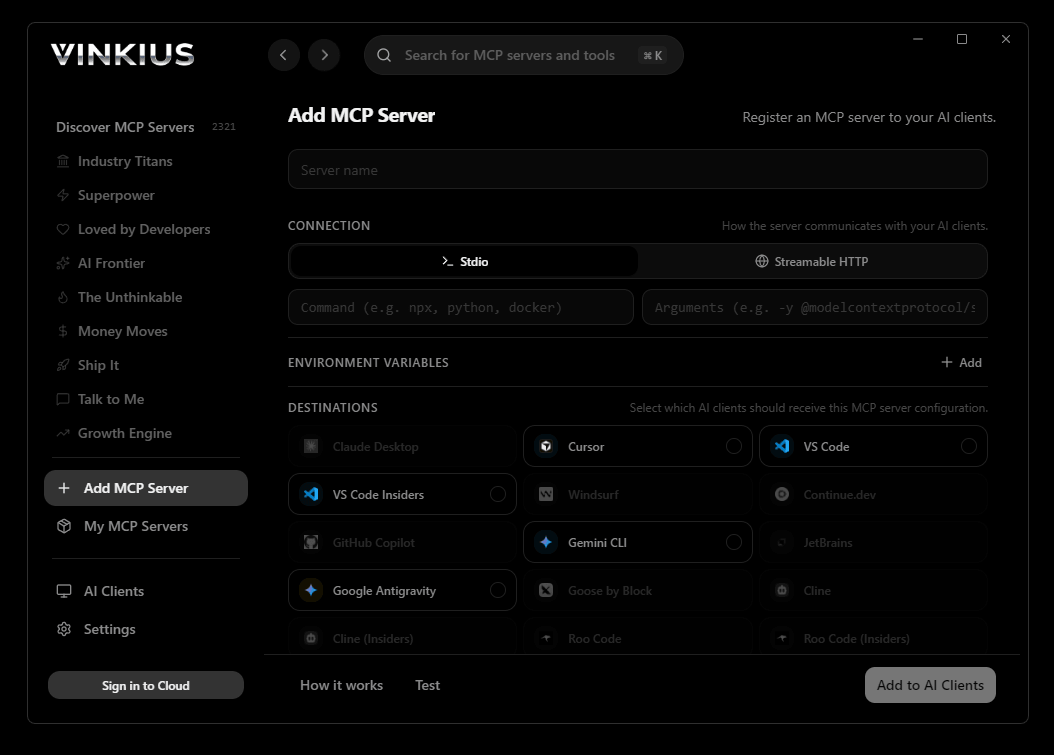
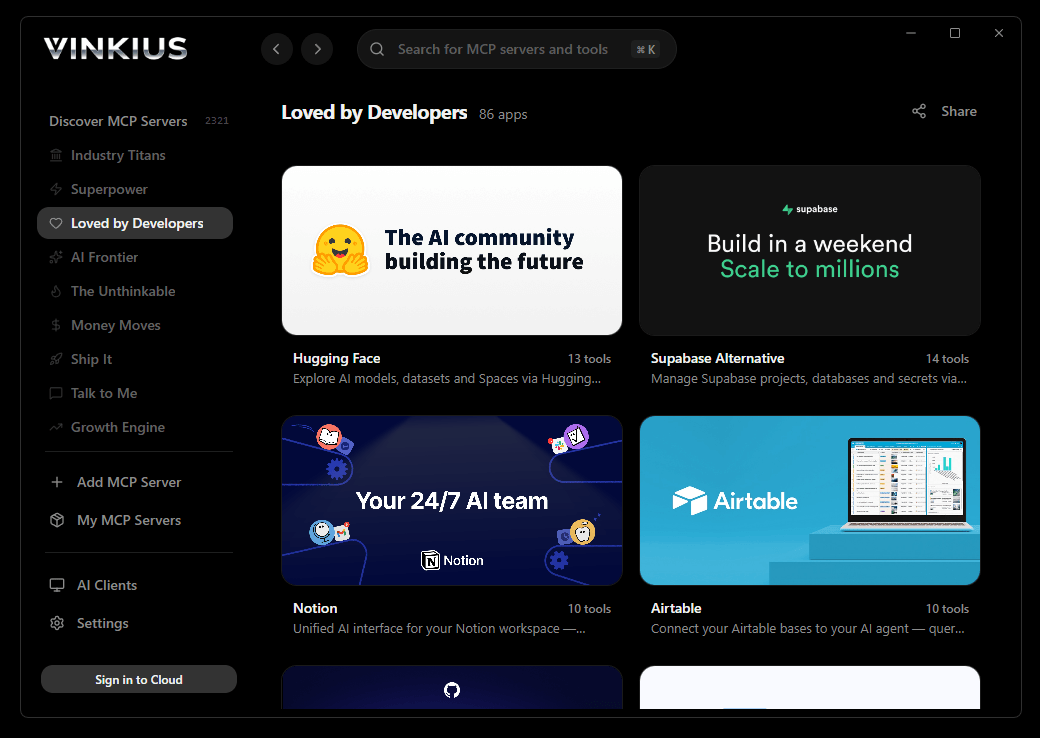
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Cloudflare and 2,500+ MCP Servers from a single visual interface.

# Your Vinkius token — get it at cloud.vinkius.com
claude mcp add cloudflare --transport http "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Cloudflare MCP Server
What you can do
Connect AI agents to Cloudflare's platform for comprehensive edge infrastructure management:
Claude Code registers Cloudflare as an MCP server in a single terminal command. Once connected, Claude Code discovers all 25 tools at runtime and can call them headlessly — ideal for CI/CD pipelines, cron jobs, and automated workflows where Cloudflare data drives decisions without human intervention.
- Manage Workers — list, inspect, delete serverless functions across your account
- Control deployments — version history, immediate/gradual rollouts, rollback capabilities
- Manage secrets — create, list, and delete encrypted environment secrets securely
- Configure routes — URL patterns that trigger Workers at specific paths or domains
- Query KV storage — read/write key-value pairs from Workers KV namespaces
- Execute D1 queries — run SQL queries against Cloudflare's serverless SQLite databases
- Inspect R2 buckets — list and manage object storage buckets
- Monitor analytics — zone traffic, Worker invocations, CPU usage, and error rates
- Tail Worker logs — create real-time logging sessions for debugging in production
- Purge CDN cache — clear cached content to serve fresh origin data
The Cloudflare MCP Server exposes 25 tools through the Vinkius. Connect it to Claude Code in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Cloudflare to Claude Code via MCP
Follow these steps to integrate the Cloudflare MCP Server with Claude Code.
Install Claude Code
Run npm install -g @anthropic-ai/claude-code if not already installed
Add the MCP Server
Run the command above in your terminal
Verify the connection
Run claude mcp to list connected servers, or type /mcp inside a session
Start using Cloudflare
Ask Claude: "Using Cloudflare, show me..." — 25 tools are ready
Why Use Claude Code with the Cloudflare MCP Server
Claude Code provides unique advantages when paired with Cloudflare through the Model Context Protocol.
Single-command setup: `claude mcp add` registers the server instantly — no config files to edit or applications to restart
Terminal-native workflow means MCP tools integrate seamlessly into shell scripts, CI/CD pipelines, and automated DevOps tasks
Claude Code runs headlessly, enabling unattended batch processing using Cloudflare tools in cron jobs or deployment scripts
Built by the same team that created the MCP protocol, ensuring first-class compatibility and the fastest adoption of new protocol features
Cloudflare + Claude Code Use Cases
Practical scenarios where Claude Code combined with the Cloudflare MCP Server delivers measurable value.
CI/CD integration: embed Cloudflare tool calls in your deployment pipeline to validate configurations or fetch secrets before shipping
Headless batch processing: schedule Claude Code to query Cloudflare nightly and generate reports without human intervention
Shell scripting: pipe Cloudflare outputs into other CLI tools for data transformation, filtering, and aggregation
Infrastructure monitoring: run Claude Code in a cron job to query Cloudflare status endpoints and alert on anomalies
Cloudflare MCP Tools for Claude Code (25)
These 25 tools become available when you connect Cloudflare to Claude Code via MCP:
create_deployment
Strategy can be immediate (100% traffic immediately) or gradual (percentage-based rollout). Requires script name, version ID, and deployment strategy. Use this to roll out new features, rollback to previous versions, or perform canary deployments. Deploy a specific Worker version to traffic
create_secret
Secrets are encrypted at rest and injected at runtime. Requires script name, secret name, and secret value. Common use: API keys, database passwords, OAuth tokens. The secret becomes available via env.VARIABLE_NAME in your Worker code. Create or update a secret for a Cloudflare Worker
create_tail_session
log() output and exceptions. Returns a tail ID and WebSocket URL for streaming logs. Use this for debugging Workers in production or monitoring error output. Create a tail logging session for a Cloudflare Worker
create_worker_route
Requires zone ID, URL pattern (e.g., "example.com/api/*"), and script name. Use this to expose your Worker at specific URL paths or domains. Create a new route pattern for a Cloudflare Worker
delete_secret
Use this to clean up unused secrets or rotate credentials. Requires script name and secret name. After deletion, the Worker will no longer have access to the secret value. Delete a secret from a Cloudflare Worker
delete_tail_session
Requires script name and tail ID. Use this to clean up unused tail sessions when debugging is complete. Delete a tail logging session for a Cloudflare Worker
delete_worker
This action cannot be undone. Requires the script name. Confirm with the user before proceeding. Delete a Cloudflare Worker script and all its associated resources
delete_worker_route
Use this to stop serving a Worker at specific URLs. Requires zone ID and route ID. Delete a route pattern from a Cloudflare Worker
get_kv_key
Returns the raw value as JSON. Use this to read configuration values, cached responses, or user data stored in KV. Get the value of a specific key in a KV namespace
get_worker
Requires the script name from list_workers results. Use this to review Worker configuration before making updates or debugging. Get detailed information about a specific Cloudflare Worker
get_worker_analytics
Returns data for recent invocations. Use this to monitor Worker performance, identify errors, or track usage trends. Get analytics data for a specific Cloudflare Worker
get_worker_version
Requires script name and version ID from list_worker_versions results. Use this to audit version contents or prepare for rollback deployment. Get detailed information about a specific Worker version
get_zone_analytics
Returns aggregated data for the last 24 hours. Use this to monitor traffic patterns, identify spikes, or measure CDN performance. Get analytics data for a specific Cloudflare zone
list_d1_databases
Returns database IDs, names, creation dates, and file sizes. Use this to identify available databases before querying. List all D1 databases in your Cloudflare account
list_deployments
Returns deployment IDs, version IDs, strategies (immediate, gradual), creation dates, and traffic percentages. Use this to review current deployment state, monitor gradual rollouts, or identify which version is live. List all deployments for a specific Cloudflare Worker
list_kv_keys
Returns key names, expiration metadata, and sizes. Use this to audit stored data or find specific keys before reading values. List all keys in a specific KV namespace
list_kv_namespaces
KV namespaces are key-value stores for Workers. Returns namespace IDs, titles, and creation dates. Use this to identify which namespaces exist before reading/writing data. List all KV namespaces in your Cloudflare account
list_r2_buckets
Returns bucket names, creation dates, and storage locations. Use this to identify available storage buckets before managing objects. List all R2 storage buckets in your Cloudflare account
list_secrets
Returns secret names and types (secret_text, secret_key). Secret values are never returned for security. Use this to audit which secrets are configured before adding new ones or cleaning up unused secrets. List all secrets for a specific Cloudflare Worker
list_worker_routes
Returns route patterns, associated script names, and zone IDs. Use this to understand which URLs invoke your Worker before adding or removing routes. List all route patterns associated with a Cloudflare Worker
list_worker_versions
Each version represents a deployed code snapshot with unique ID, creation date, and metadata. Returns version IDs, timestamps, and author information. Use this to review deployment history, rollback to previous versions, or audit code changes. List all versions of a specific Cloudflare Worker
list_workers
Returns script names, creation dates, modification dates, and deployment status. Use this as the first step to identify which Workers exist before managing versions, deployments, or secrets. List all Cloudflare Workers scripts in your account
list_zones
Returns zone IDs, domain names, status, plan, and name servers. Use this to identify zone IDs needed for Worker routes, DNS management, or cache operations. List all DNS zones in your Cloudflare account
purge_cache
Use this after deploying content changes or updating static assets. Requires zone ID. Purge all cached content for a specific zone
query_d1
Supports SELECT, INSERT, UPDATE, DELETE operations. Returns query results as JSON. Use this for data analysis, migrations, or ad-hoc queries. Requires database ID and SQL query string. Execute a SQL query against a D1 database
Example Prompts for Cloudflare in Claude Code
Ready-to-use prompts you can give your Claude Code agent to start working with Cloudflare immediately.
"List all serverless Cloudflare Workers deployed natively bound to my account."
"Query the KV namespace assigned to 'production_keys' and extract the specific text mapping 'gateway_url'."
"Check error statistics on my main D1 SQLite database instance over the last 24 hours."
Troubleshooting Cloudflare MCP Server with Claude Code
Common issues when connecting Cloudflare to Claude Code through the Vinkius, and how to resolve them.
Command not found: claude
npm install -g @anthropic-ai/claude-codeConnection timeout
Cloudflare + Claude Code FAQ
Common questions about integrating Cloudflare MCP Server with Claude Code.
How do I add an MCP server to Claude Code?
claude mcp add --transport http "" in your terminal. Claude Code registers the server and discovers all tools immediately.Can Claude Code run MCP tools in headless mode?
How do I list all connected MCP servers?
claude mcp in your terminal to see all registered servers and their status, or type /mcp inside an active Claude Code session.Connect Cloudflare with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Cloudflare to Claude Code
Get your token, paste the configuration, and start using 25 tools in under 2 minutes. No API key management needed.
