CyberArk Privilege Cloud MCP Server for Claude Code 10 tools — connect in under 2 minutes
Claude Code is Anthropic's agentic CLI for terminal-first development. Add CyberArk Privilege Cloud as an MCP server in one command and Claude Code will discover every tool at runtime — ideal for automation pipelines, CI/CD integration, and headless workflows via the Vinkius.
ASK AI ABOUT THIS MCP SERVER
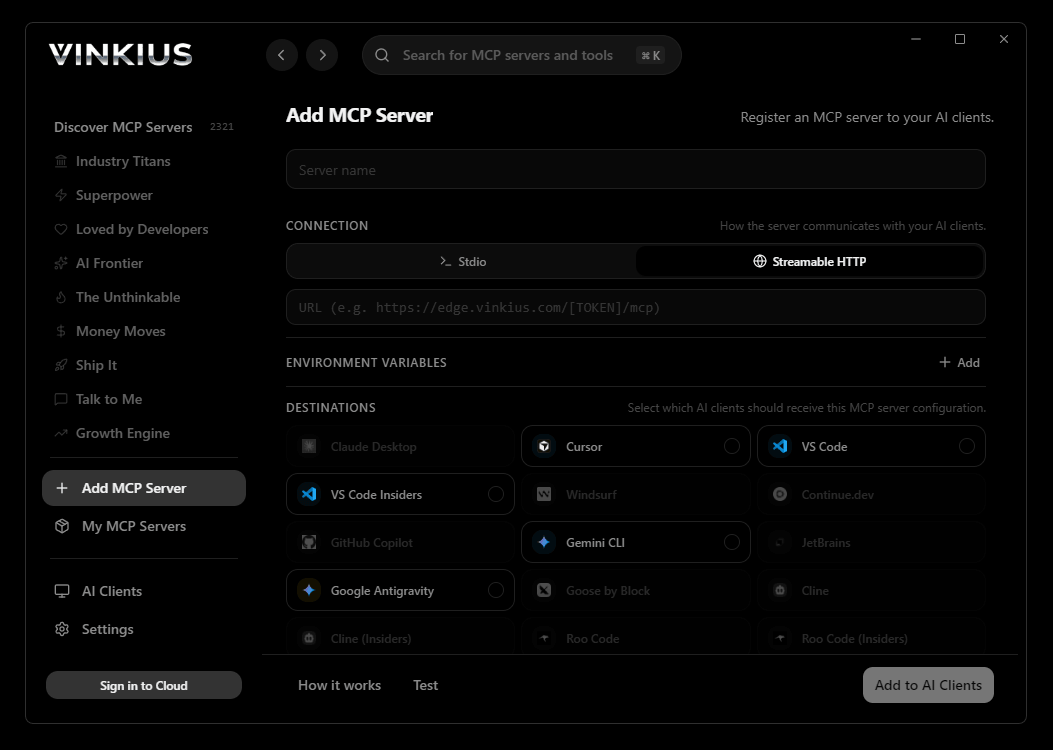
Vinkius supports streamable HTTP and SSE.
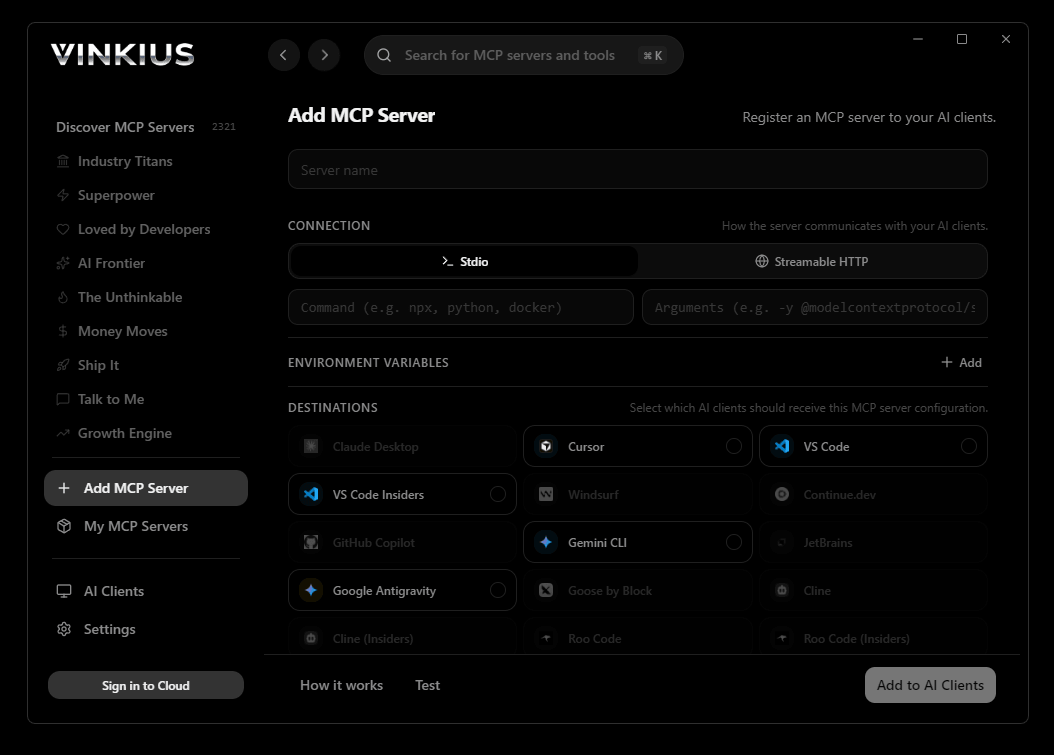
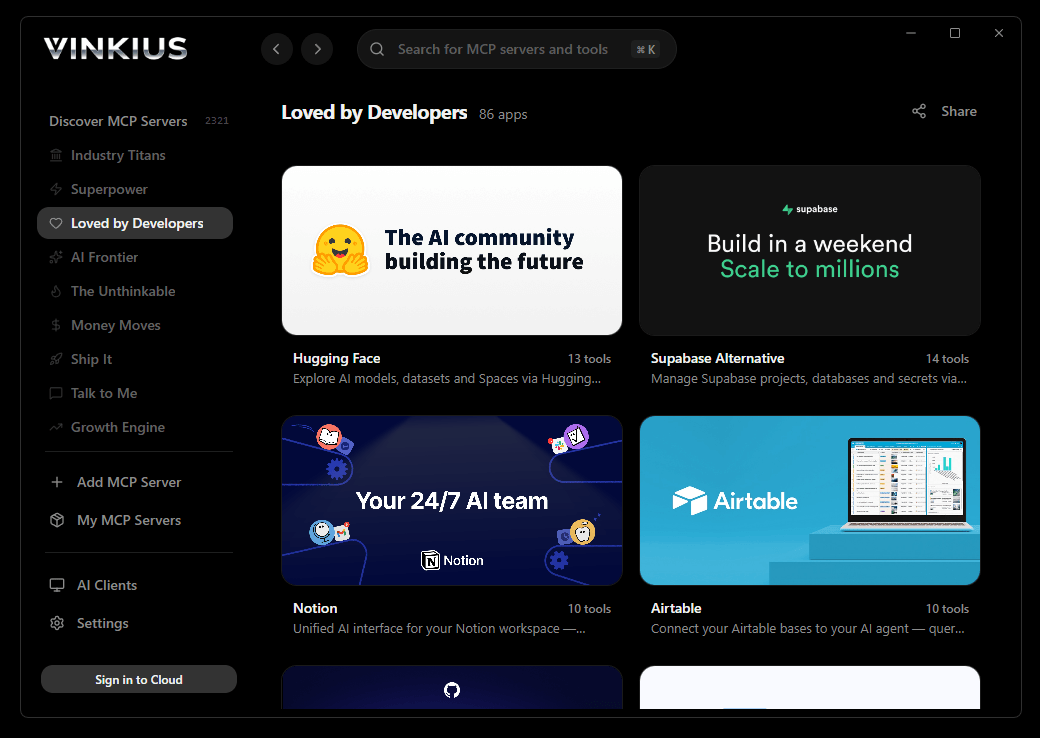
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install CyberArk Privilege Cloud and 2,500+ MCP Servers from a single visual interface.

# Your Vinkius token — get it at cloud.vinkius.com
claude mcp add cyberark-privilege-cloud --transport http "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About CyberArk Privilege Cloud MCP Server
Connect your CyberArk Privilege Cloud account to any AI agent and take full control of your identity security and privileged access management through natural conversation.
Claude Code registers CyberArk Privilege Cloud as an MCP server in a single terminal command. Once connected, Claude Code discovers all 10 tools at runtime and can call them headlessly — ideal for CI/CD pipelines, cron jobs, and automated workflows where CyberArk Privilege Cloud data drives decisions without human intervention.
What you can do
- Safe Orchestration — List secure Safes and retrieve intricate settings including retention periods and assigned Central Policy Managers (CPM)
- Privileged Account Management — Enumerate vaulted credentials (Root, Administrator, Service Accounts) and audit rotational statuses and address mappings
- Password Retrieval (Check-out) — Pull actual secrets from the Vault with mandatory audited justifications, allowing the agent to securely retrieve credentials for incident response
- Identity Oversight — List internal and LDAP-mapped directory users and groups to verify PAM logical access architectures and RBAC rules
- Session Control — Forcibly terminate active PSM/PSMP privileged sessions instantly as an active incident response mechanism
- Vault Onboarding — Provision new privileged accounts into secure Safes by mapping them to specific platform IDs for automated rotation lifecycle management
The CyberArk Privilege Cloud MCP Server exposes 10 tools through the Vinkius. Connect it to Claude Code in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect CyberArk Privilege Cloud to Claude Code via MCP
Follow these steps to integrate the CyberArk Privilege Cloud MCP Server with Claude Code.
Install Claude Code
Run npm install -g @anthropic-ai/claude-code if not already installed
Add the MCP Server
Run the command above in your terminal
Verify the connection
Run claude mcp to list connected servers, or type /mcp inside a session
Start using CyberArk Privilege Cloud
Ask Claude: "Using CyberArk Privilege Cloud, show me..." — 10 tools are ready
Why Use Claude Code with the CyberArk Privilege Cloud MCP Server
Claude Code provides unique advantages when paired with CyberArk Privilege Cloud through the Model Context Protocol.
Single-command setup: `claude mcp add` registers the server instantly — no config files to edit or applications to restart
Terminal-native workflow means MCP tools integrate seamlessly into shell scripts, CI/CD pipelines, and automated DevOps tasks
Claude Code runs headlessly, enabling unattended batch processing using CyberArk Privilege Cloud tools in cron jobs or deployment scripts
Built by the same team that created the MCP protocol, ensuring first-class compatibility and the fastest adoption of new protocol features
CyberArk Privilege Cloud + Claude Code Use Cases
Practical scenarios where Claude Code combined with the CyberArk Privilege Cloud MCP Server delivers measurable value.
CI/CD integration: embed CyberArk Privilege Cloud tool calls in your deployment pipeline to validate configurations or fetch secrets before shipping
Headless batch processing: schedule Claude Code to query CyberArk Privilege Cloud nightly and generate reports without human intervention
Shell scripting: pipe CyberArk Privilege Cloud outputs into other CLI tools for data transformation, filtering, and aggregation
Infrastructure monitoring: run Claude Code in a cron job to query CyberArk Privilege Cloud status endpoints and alert on anomalies
CyberArk Privilege Cloud MCP Tools for Claude Code (10)
These 10 tools become available when you connect CyberArk Privilege Cloud to Claude Code via MCP:
add_account
Requires precise mapping to an underlying Platform ID (e.g., WinDesktopLocal, UnixSSH) which dictates how CyberArk rotates and verifies the credential moving forward. Provision a new privileged account into a Vault Safe
delete_account
Requires high authorization. Used during system decommissioning so the CPM stops attempting failed password rotations. Delete a privileged account from the CyberArk Vault
get_account
Necessary before rotating or interacting with an account. Get detailed properties for a specific vaulted account
get_safe
Get details and metadata for a specific PAM Safe
list_accounts
These represent highly sensitive credentials (Root, Administrator, Service Accounts). Includes the bounding platform, Safe allocation, address, and rotational status. Use the search string to narrow targets. Search and list privileged accounts vaulted in CyberArk
list_groups
Permissions to Safes are canonically granted to Groups rather than individual users to enforce RBAC best practices. Used to verify PAM logical access architectures. List CyberArk Vault User Groups
list_safes
Safes are the fundamental logical containers separating credentials physically and logically. Required to locate where specific critical tier-0 credentials or local admin passwords reside. List all secure Safes in CyberArk Privileged Access Manager
list_users
Identifies active vault administrators, auditors, and human end-users consuming PSM (Privileged Session Manager) sessions. List all CyberArk users (local and synchronized)
retrieve_password
Highly audited endpoint triggering SIEM alerts. A justification reason is mandatory. After retrieval, exclusive access platforms may lock the credential until check-in or auto-rotation. Retrieve the clear-text password for an account (check-out)
terminate_session
Used as an active incident response mechanism if a SOC analyst or anomalous behavior engine detects unauthorized actions mid-session. Forcibly terminate an active Privileged Session (PSM/PSMP)
Example Prompts for CyberArk Privilege Cloud in Claude Code
Ready-to-use prompts you can give your Claude Code agent to start working with CyberArk Privilege Cloud immediately.
"List all privileged accounts for address '10.0.0.1'"
"Retrieve password for account 123. Reason: 'Emergency DB maintenance'"
"Terminate active session 'sess_abc'"
Troubleshooting CyberArk Privilege Cloud MCP Server with Claude Code
Common issues when connecting CyberArk Privilege Cloud to Claude Code through the Vinkius, and how to resolve them.
Command not found: claude
npm install -g @anthropic-ai/claude-codeConnection timeout
CyberArk Privilege Cloud + Claude Code FAQ
Common questions about integrating CyberArk Privilege Cloud MCP Server with Claude Code.
How do I add an MCP server to Claude Code?
claude mcp add --transport http "" in your terminal. Claude Code registers the server and discovers all tools immediately.Can Claude Code run MCP tools in headless mode?
How do I list all connected MCP servers?
claude mcp in your terminal to see all registered servers and their status, or type /mcp inside an active Claude Code session.Connect CyberArk Privilege Cloud with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect CyberArk Privilege Cloud to Claude Code
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
