Drata MCP Server for Pydantic AI 10 tools — connect in under 2 minutes
Pydantic AI brings type-safe agent development to Python with first-class MCP support. Connect Drata through Vinkius and every tool is automatically validated against Pydantic schemas. catch errors at build time, not in production.
ASK AI ABOUT THIS MCP SERVER
Vinkius supports streamable HTTP and SSE.
import asyncio
from pydantic_ai import Agent
from pydantic_ai.mcp import MCPServerHTTP
async def main():
# Your Vinkius token. get it at cloud.vinkius.com
server = MCPServerHTTP(url="https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp")
agent = Agent(
model="openai:gpt-4o",
mcp_servers=[server],
system_prompt=(
"You are an assistant with access to Drata "
"(10 tools)."
),
)
result = await agent.run(
"What tools are available in Drata?"
)
print(result.data)
asyncio.run(main())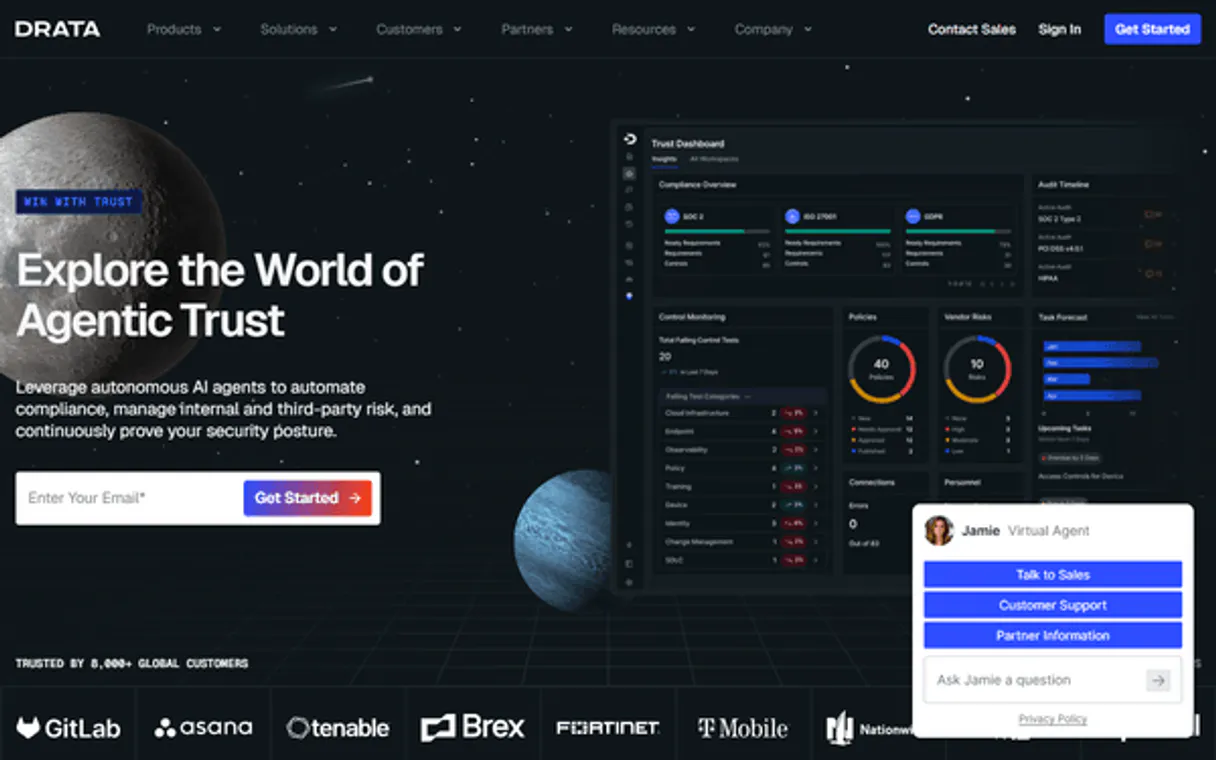
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Drata MCP Server
Connect your Drata account to any AI agent and take full control of your continuous compliance and automated security monitoring through natural conversation.
Pydantic AI validates every Drata tool response against typed schemas, catching data inconsistencies at build time. Connect 10 tools through Vinkius and switch between OpenAI, Anthropic, or Gemini without changing your integration code. full type safety, structured output guarantees, and dependency injection for testable agents.
What you can do
- Compliance Control Oversight — List internal compliance controls and fetch exact evaluation states to see if technical or administrative requirements are passing or failing
- Personnel Compliance Tracking — Monitor employee and contractor directories to identify missing security training, background checks, or policy acknowledgments
- Security Policy Auditing — Retrieve the overarching InfoSec documentation and extract renewal dates and completion rates to assess audit readiness
- Automated Test Monitoring — Detail which technical monitors across AWS, GCP, or Azure are triggering compliance deviations in real-time
- Framework Readiness — Track active compliance frameworks (SOC 2, ISO 27001, HIPAA) and get overall readiness scores and control completion percentages
- Vendor Risk Management — Returns the vendor risk inventory to track security questionnaires and data risk classifications for third-party subprocessors
- Cloud Asset Verification — Insight into how EC2, RDS, and other infrastructure nodes align against underlying compliance controls
The Drata MCP Server exposes 10 tools through the Vinkius. Connect it to Pydantic AI in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Drata to Pydantic AI via MCP
Follow these steps to integrate the Drata MCP Server with Pydantic AI.
Install Pydantic AI
Run pip install pydantic-ai
Replace the token
Replace [YOUR_TOKEN_HERE] with your Vinkius token
Run the agent
Save to agent.py and run: python agent.py
Explore tools
The agent discovers 10 tools from Drata with type-safe schemas
Why Use Pydantic AI with the Drata MCP Server
Pydantic AI provides unique advantages when paired with Drata through the Model Context Protocol.
Full type safety: every MCP tool response is validated against Pydantic models, catching data inconsistencies before they reach your application
Model-agnostic architecture. switch between OpenAI, Anthropic, or Gemini without changing your Drata integration code
Structured output guarantee: Pydantic AI ensures tool results conform to defined schemas, eliminating runtime type errors
Dependency injection system cleanly separates your Drata connection logic from agent behavior for testable, maintainable code
Drata + Pydantic AI Use Cases
Practical scenarios where Pydantic AI combined with the Drata MCP Server delivers measurable value.
Type-safe data pipelines: query Drata with guaranteed response schemas, feeding validated data into downstream processing
API orchestration: chain multiple Drata tool calls with Pydantic validation at each step to ensure data integrity end-to-end
Production monitoring: build validated alert agents that query Drata and output structured, schema-compliant notifications
Testing and QA: use Pydantic AI's dependency injection to mock Drata responses and write comprehensive agent tests
Drata MCP Tools for Pydantic AI (10)
These 10 tools become available when you connect Drata to Pydantic AI via MCP:
drata_get_control
Returns passing/failing status, which automated tests provide evidence for this control, the explicit auditor language defining the risk logic, and any manual evidence uploads. Use to investigate why a control is failing, what evidence supports it, or to prepare for auditor questions about a specific requirement. Get detailed status of a specific Drata control — pass/fail state, automated test evidence, and auditor-facing risk language
drata_get_person
Returns MDM (Jamf/Intune) enrollment status, background check clearance date, onboarding milestone completion, linked IdP (Okta/Google Workspace) groups for access control mapping, security training completion date, and any compliance gaps. Use when investigating a specific employee compliance issue. Get the compliance onboarding state of a specific employee — MDM enrollment, background checks, IdP grouping, and training milestones
drata_get_policy
Essential for assessing audit readiness regarding mandatory annual document refreshes. Get detailed status of a specific Drata policy — renewal dates, employee acknowledgment rates, owner assignment, and version history
drata_list_assets
Each asset shows: resource type, resource ID, compliance status against linked controls, encryption-at-rest verification, network boundary adherence, and associated region/VPC. Use when the user asks about infrastructure compliance, unencrypted resources, or needs an asset inventory for audit evidence. List cloud infrastructure assets monitored by Drata — EC2 instances, RDS databases, S3 buckets, and other resources with compliance status
drata_list_controls
Each control represents a specific requirement (e.g., "Passwords must be 12+ characters", "MFA enabled for all users", "Encryption at rest required"). Returns control name, description, passing/failing status, mapped framework(s), linked tests, and control owner. Use when the user asks about compliance posture, failing controls, or audit gap analysis. List all compliance controls in Drata — the discrete technical and administrative requirements mapped to SOC 2, ISO 27001, HIPAA, and GDPR frameworks
drata_list_frameworks
Each framework shows: name, version, overall readiness score, percentage of controls passing, number of controls mapped, and target audit date. Provides a high-level view of multi-framework compliance posture. Use for board-level reporting, audit planning, or determining which framework needs the most attention. List active compliance frameworks tracked by the Drata workspace — SOC 2 Type II, ISO 27001, HIPAA, GDPR, PCI DSS — with readiness scores
drata_list_personnel
Each person includes: name, email, role, employment type, Security Awareness Training status (completed/overdue/not started), device compliance (MDM enrolled, encrypted, antivirus), background check clearance, and policy acceptance rates. Use for "who is non-compliant?", "which employees have overdue training?", or pre-audit personnel reporting. List all tracked personnel in Drata with security training status, device compliance, background check clearance, and policy acceptance
drata_list_policies
Each policy includes: name, category, CISO approval status, version number, last review date, next review due, and employee acknowledgment completion rate. Policies are mandatory for SOC 2 / ISO 27001. Use when the user asks about policy status, which policies need review, or audit readiness regarding documentation. List all security and compliance policies in Drata — Information Security, Data Classification, Incident Response, Acceptable Use, and more
drata_list_tests
Each test monitors a specific technical requirement in real-time (e.g., "S3 Buckets must not be public", "GitHub branch protection enabled", "MFA enforced in Okta"). Shows test name, associated control, pass/fail status, last evaluation time, and failing resources if any. Use when the user asks about automated monitoring, which checks are failing, or real-time compliance status. List Drata automated continuous compliance tests — real-time monitors checking AWS, GitHub, Okta, and other integrations for security deviations
drata_list_vendors
Each vendor includes: company name, data risk classification (Critical/High/Medium/Low), security questionnaire completion status, SOC 2 report review status, last assessment date, data categories shared, and assigned risk owner. Use for vendor risk assessment, subprocessor audits, or evaluating the security posture of your supply chain. List third-party vendors in Drata vendor risk management — risk classification, security questionnaire status, and SOC 2 report reviews
Example Prompts for Drata in Pydantic AI
Ready-to-use prompts you can give your Pydantic AI agent to start working with Drata immediately.
"Show me all failing compliance controls"
"What is the compliance onboarding status for employee John Doe?"
"List my active compliance frameworks and readiness scores"
Troubleshooting Drata MCP Server with Pydantic AI
Common issues when connecting Drata to Pydantic AI through the Vinkius, and how to resolve them.
MCPServerHTTP not found
pip install --upgrade pydantic-aiDrata + Pydantic AI FAQ
Common questions about integrating Drata MCP Server with Pydantic AI.
How does Pydantic AI discover MCP tools?
MCPServerHTTP instance with the server URL. Pydantic AI connects, discovers all tools, and generates typed Python interfaces automatically.Does Pydantic AI validate MCP tool responses?
Can I switch LLM providers without changing MCP code?
Connect Drata with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Drata to Pydantic AI
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
