Elastic Security MCP Server for Cursor 10 tools — connect in under 2 minutes
Cursor is an AI-first code editor built on VS Code that integrates LLM-powered coding assistance directly into the development workflow. Its Agent mode enables autonomous multi-step coding tasks, and MCP support lets agents access external data sources and APIs during code generation.
ASK AI ABOUT THIS MCP SERVER
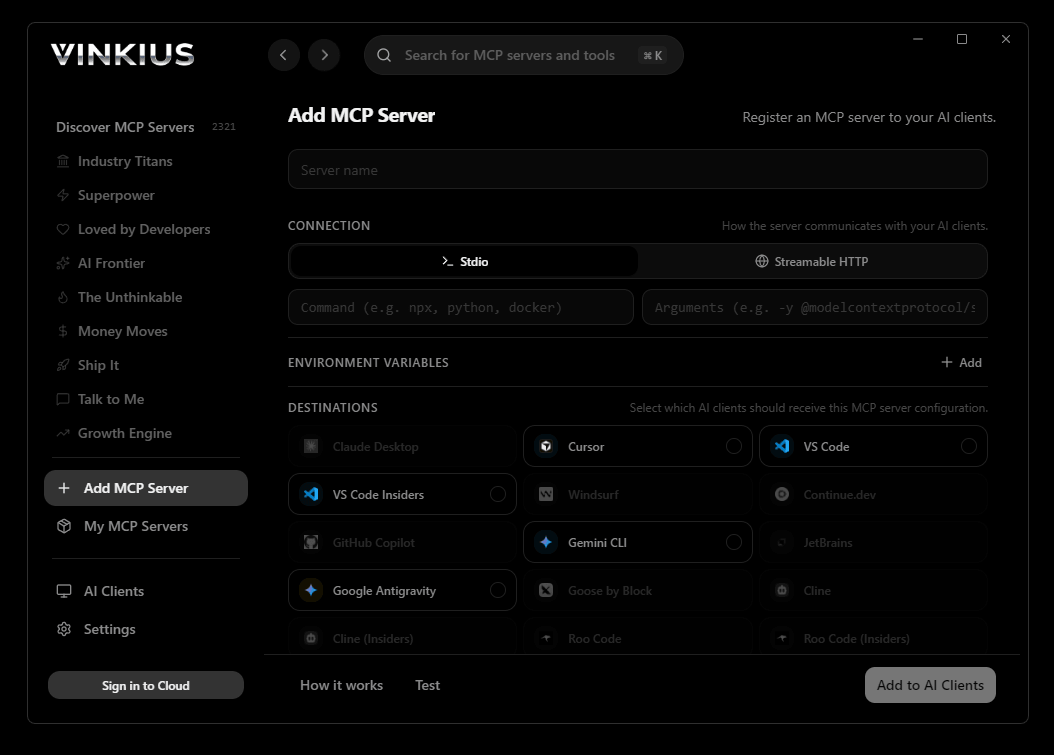
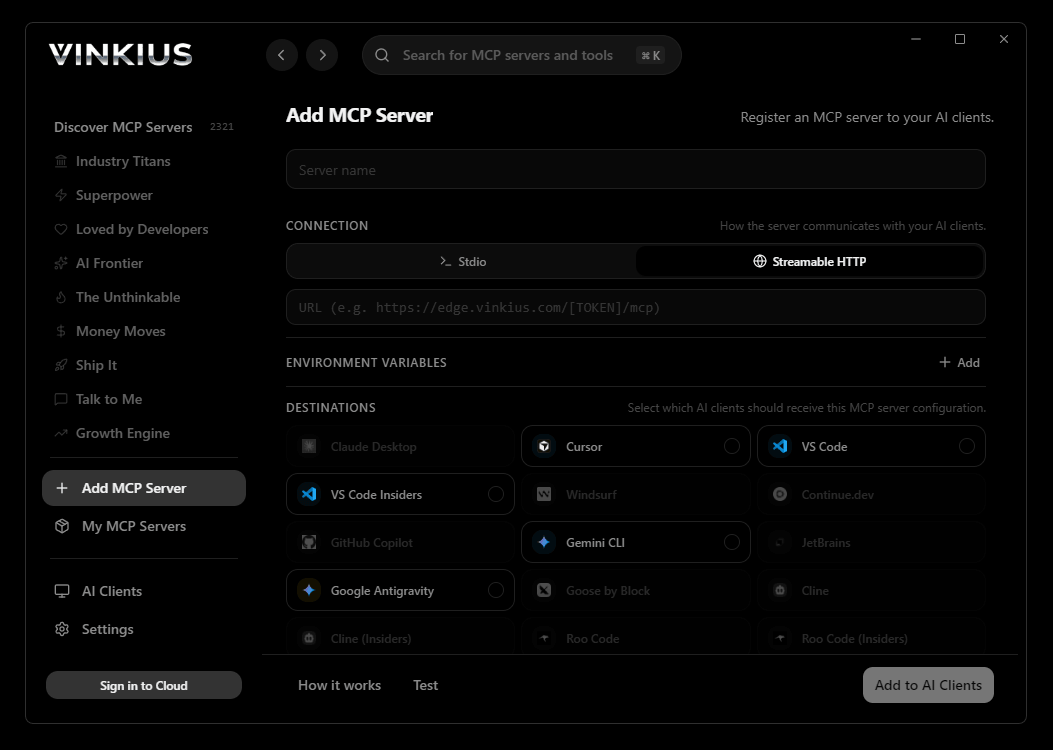
Vinkius supports streamable HTTP and SSE.
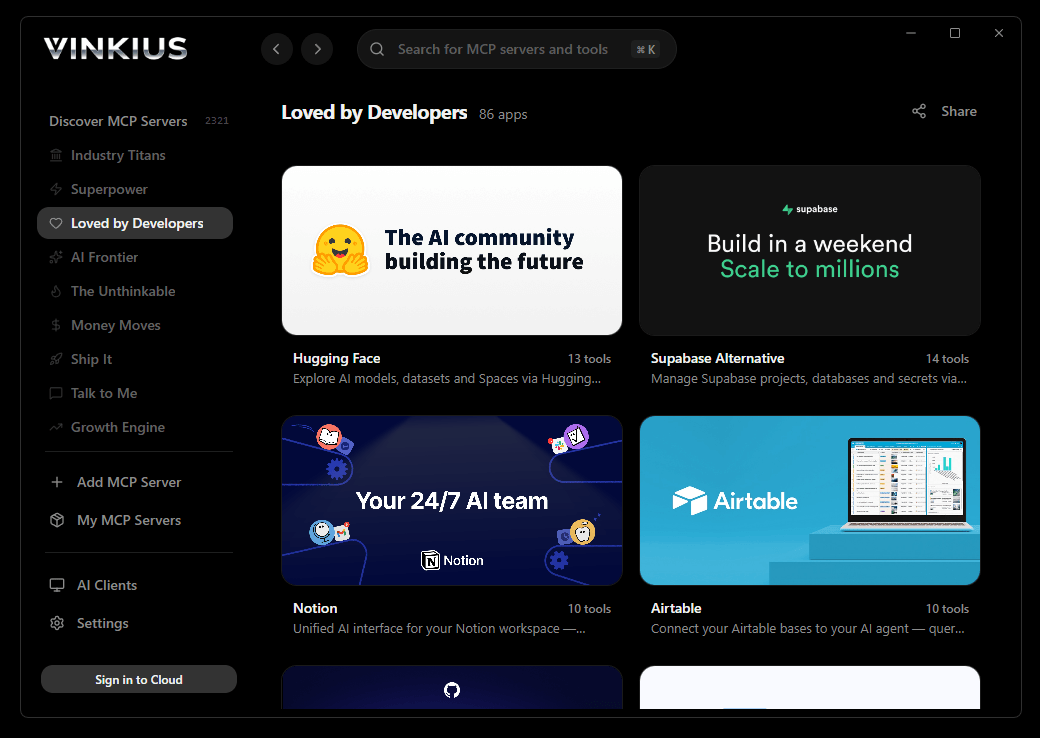
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Elastic Security and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"elastic-security": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Elastic Security MCP Server
Connect your Elastic Security (SIEM) deployment to any AI agent and take full control of your threat detection and SOC auditing through natural conversation.
Cursor's Agent mode turns Elastic Security into an in-editor superpower. Ask Cursor to generate code using live data from Elastic Security and it fetches, processes, and writes — all in a single agentic loop. 10 tools appear alongside file editing and terminal access, creating a unified development environment grounded in real-time information.
What you can do
- Detection Rule Orchestration — List all configured detection rules and retrieve exact EQL or KQL statements to map MITRE ATT&CK coverage natively
- Live Alert Auditing — Search raw generated security signals (alerts) consolidating hostname, user profiles, and IP geolocations into a single view
- Rule Lifecycle Management — Create new custom log detection rules or irreversibly purge custom logic from the Kibana SIEM engine to tune your environment
- Exception & Whitelisting — List global exception lists and whitelist hostnames inside existing containers to resolve false positives and noise in real-time
- Threat Intel Verification — Search for specific rules by name, tag, or MITRE tactic to expedite SOC auditing for newly reported CVEs or ransomware
- State Control — Enable or disable existing detection rules to manage noisy triggers across large organizational units seamlessly
- System Health Checks — Verify if official Elastic prepackaged rules need updates to ensure lack of latest official threat models is addressed
The Elastic Security MCP Server exposes 10 tools through the Vinkius. Connect it to Cursor in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Elastic Security to Cursor via MCP
Follow these steps to integrate the Elastic Security MCP Server with Cursor.
Open MCP Settings
Press Cmd+Shift+P (macOS) or Ctrl+Shift+P (Windows/Linux) → search "MCP Settings"
Add the server config
Paste the JSON configuration above into the mcp.json file that opens
Save the file
Cursor will automatically detect the new MCP server
Start using Elastic Security
Open Agent mode in chat and ask: "Using Elastic Security, help me..." — 10 tools available
Why Use Cursor with the Elastic Security MCP Server
Cursor AI Code Editor provides unique advantages when paired with Elastic Security through the Model Context Protocol.
Agent mode turns Cursor into an autonomous coding assistant that can read files, run commands, and call MCP tools without switching context
Cursor's Composer feature can generate entire files using real-time data fetched through MCP — no copy-pasting from external dashboards
MCP tools appear alongside built-in tools like file reading and terminal access, creating a unified agentic environment
VS Code extension compatibility means your existing workflow, keybindings, and extensions all work alongside MCP tools
Elastic Security + Cursor Use Cases
Practical scenarios where Cursor combined with the Elastic Security MCP Server delivers measurable value.
Code generation with live data: ask Cursor to generate a security report module using live DNS and subdomain data fetched through MCP
Automated documentation: have Cursor query your API's tool schemas and generate TypeScript interfaces or OpenAPI specs automatically
Infrastructure-as-code: Cursor can fetch domain configurations and generate corresponding Terraform or CloudFormation templates
Test scaffolding: ask Cursor to pull real API responses via MCP and generate unit test fixtures from actual data
Elastic Security MCP Tools for Cursor (10)
These 10 tools become available when you connect Elastic Security to Cursor via MCP:
add_exception
name value to the target exception container, implicitly ignoring telemetry matched on this field for any rule bound to the list. Use explicitly to resolve false positives. Whitelist a hostname inside an existing Exception List
create_rule
Defines immediate risk scores multiplying against asset valuations, generating Elastic Signals tracking MITRE TTPs upon match. Create a new Log Detection Rule tracking malicious Elastic telemetry
delete_rule
Cannot be applied to Elastic Pre-built rules which are managed globally via package updates. Irreversible. Hard-delete a custom Elastic detection rule completely
find_detection_rules
Expedites SOC auditing when evaluating coverage for newly reported CVEs or specific localized threats. Search for specific Elastic rules by name, tag or MITRE tactic
get_prepackaged_rules_status
Identifies if the environment is lacking the latest official threat models targeting Windows, Linux, and Cloud environments. Check if official Elastic prepackaged rules need updates
get_rule
Displays run intervals, severity assignment, index scopes, and explicit reference URLs matching threat intel reports. Get exact details, intervals, and query logic for a distinct Rule
list_detection_rules
g., logs-endpoint*, winlogbeat*). Vital for mapping MITRE ATT&CK coverage against the Elastic schema. List all detection rules configured within the Elastic SIEM
list_exceptions
These lists logically bypass specific rules, preventing SIEM alerts from triggering on known-good administrative behavior like vulnerability scanners. List global exception lists managing detection bypass logic
search_signals
Signals consolidate the triggering payload structure, enriching it with Hostname, User profiles, IP geolocations, and process trees. Search raw generated Elastic Security alerts (Signals)
update_rule
Used explicitly to disable noisy rules triggering false positives across large organizational units, or to re-enable them post-tuning. Enable or Disable an existing Elastic Detection Rule
Example Prompts for Elastic Security in Cursor
Ready-to-use prompts you can give your Cursor agent to start working with Elastic Security immediately.
"Show me all active detection rules tagged with 'Ransomware'"
"Add hostname 'dev-machine-01' to exception list 'global-whitelist'"
"Search for security signals from user 'admin_root' in the last hour"
Troubleshooting Elastic Security MCP Server with Cursor
Common issues when connecting Elastic Security to Cursor through the Vinkius, and how to resolve them.
Tools not appearing in Cursor
Server shows as disconnected
Elastic Security + Cursor FAQ
Common questions about integrating Elastic Security MCP Server with Cursor.
What is Agent mode and why does it matter for MCP?
Where does Cursor store MCP configuration?
mcp.json file. You can configure servers at the project level (.cursor/mcp.json in your project root) or globally (~/.cursor/mcp.json). Project-level configs take precedence.Can Cursor use MCP tools in inline edits?
How do I verify MCP tools are loaded?
Connect Elastic Security with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Elastic Security to Cursor
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
