Okta MCP Server for Cline 10 tools — connect in under 2 minutes
Cline is an autonomous AI coding agent inside VS Code that plans, executes, and iterates on tasks. Wire Okta through Vinkius and Cline gains direct access to every tool. from data retrieval to workflow automation. without leaving the terminal.
ASK AI ABOUT THIS MCP SERVER
Vinkius supports streamable HTTP and SSE.
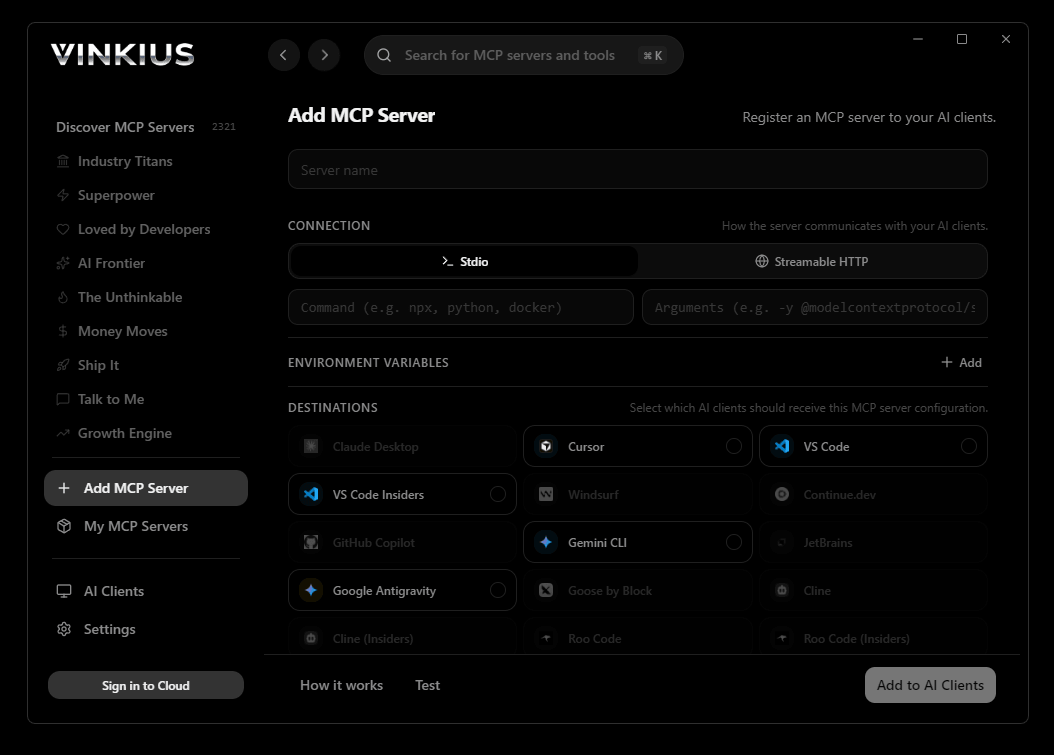
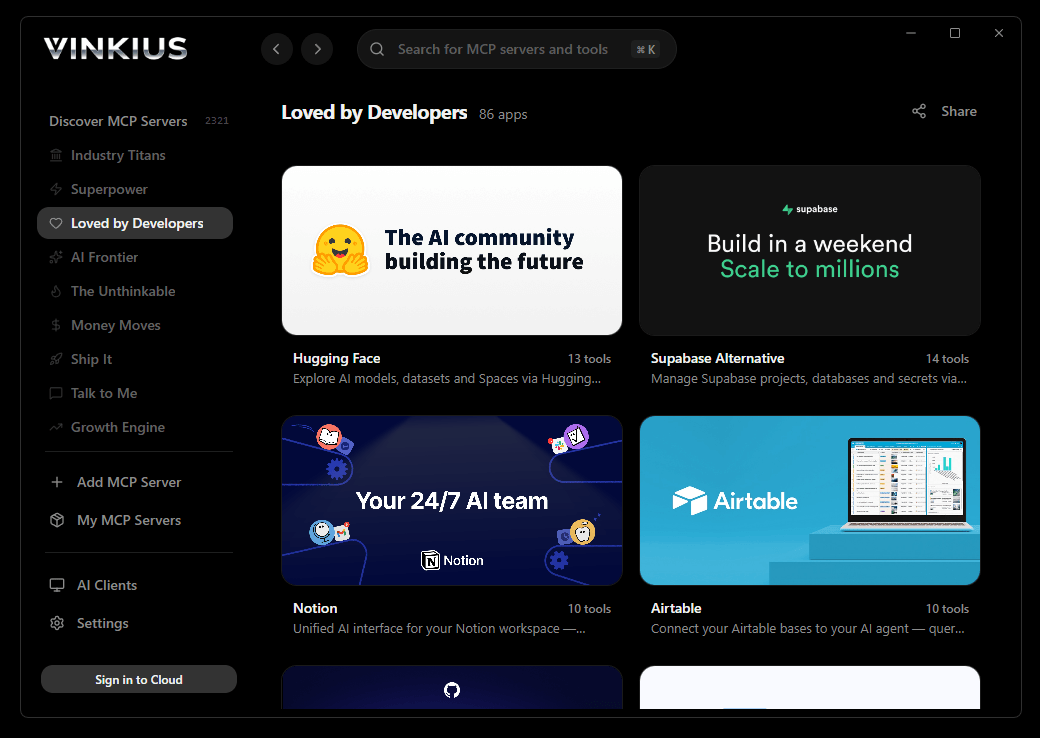
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Okta and 2,500+ MCP Servers from a single visual interface.

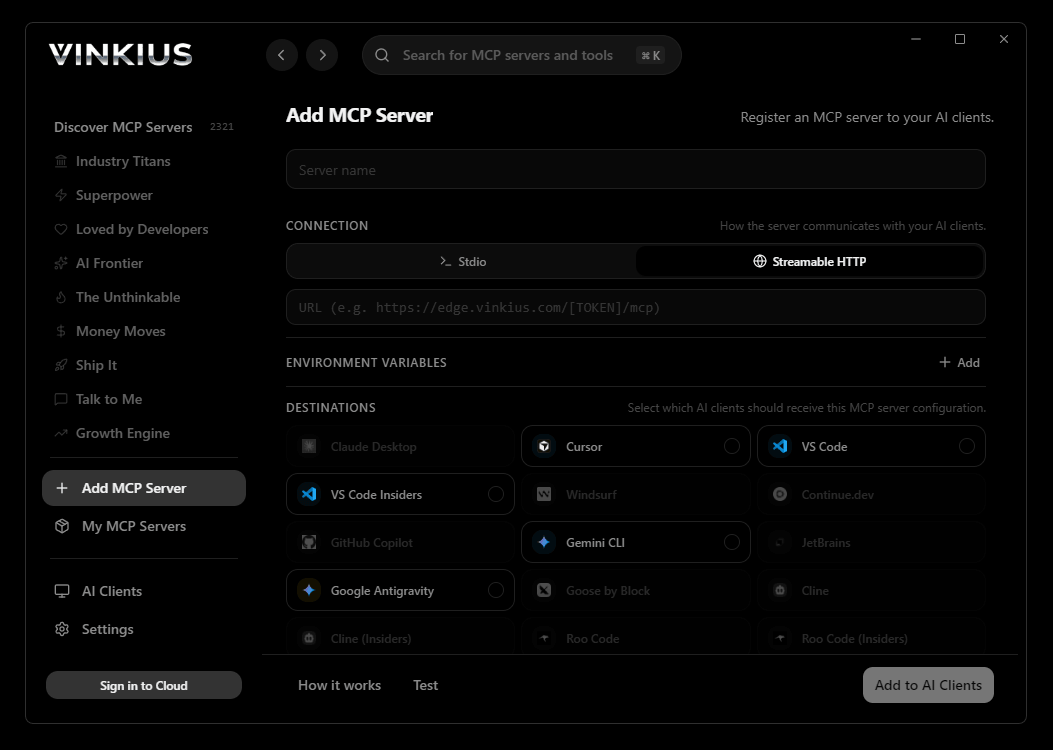
{
"mcpServers": {
"okta": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Okta MCP Server
Connect your Okta Identity Cloud instance to any AI agent to streamline identity management, user provisioning, and secure access flows. Eliminate the need to dig through administrative dashboards by interacting conversationally to create users, unblock accounts, or manage group assignments.
Cline operates autonomously inside VS Code. it reads your codebase, plans a strategy, and executes multi-step tasks including Okta tool calls without waiting for prompts between steps. Connect 10 tools through Vinkius and Cline can fetch data, generate code, and commit changes in a single autonomous run.
What you can do
- User Provisioning & Lifecycle — Interrogate the AI to list active users, retrieve specific profile details, create new identities, or cleanly deprovision departing employees
- Access Control & Troubleshooting — Instantly check a user's sign-in activity to resolve locks, reset credentials, or clear active sessions centrally
- Group Segregation — Manage departmental access by querying group directories, creating structured groups, or orchestrating bulk user assignments into logical access structures
- Application Assignment — Audit the integrations mapped to your user base, ensuring proper access to company apps based on the least-privilege principle
The Okta MCP Server exposes 10 tools through the Vinkius. Connect it to Cline in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Okta to Cline via MCP
Follow these steps to integrate the Okta MCP Server with Cline.
Open Cline MCP Settings
Click the MCP Servers icon in the Cline sidebar panel
Add remote server
Click "Add MCP Server" and paste the configuration above
Enable the server
Toggle the server switch to ON
Start using Okta
Ask Cline: "Using Okta, help me...". 10 tools available
Why Use Cline with the Okta MCP Server
Cline provides unique advantages when paired with Okta through the Model Context Protocol.
Cline operates autonomously. it reads your codebase, plans a strategy, and executes multi-step tasks including MCP tool calls without step-by-step prompts
Runs inside VS Code, so you get MCP tool access alongside your existing extensions, terminal, and version control in a single window
Cline can create, edit, and delete files based on MCP tool responses, enabling end-to-end automation from data retrieval to code generation
Transparent execution: every tool call and file change is shown in Cline's activity log for full visibility and approval before committing
Okta + Cline Use Cases
Practical scenarios where Cline combined with the Okta MCP Server delivers measurable value.
Autonomous feature building: tell Cline to fetch data from Okta and scaffold a complete module with types, handlers, and tests
Codebase refactoring: use Okta tools to validate live data while Cline restructures your code to match updated schemas
Automated testing: Cline fetches real responses from Okta and generates snapshot tests or mocks based on actual payloads
Incident response: query Okta for real-time status and let Cline generate hotfix patches based on the findings
Okta MCP Tools for Cline (10)
These 10 tools become available when you connect Okta to Cline via MCP:
clear_user_sessions
Necessary when a device is compromised. Terminate all active login sessions for a specific user
deactivate_user
This instantly converts the user status to DEPROVISIONED, permanently revoking all active sessions, killing SAML/OIDC assertions, and blocking future application access. Use for emergency offboarding. Suspend and deprovision an Okta user account immediately
get_app
Includes critical security bindings, client secrets (for OIDC), X.509 cert chains, ACS URLs, and strict token-grant lifespans. View detailed SSO configuration for a specific application
get_group
View details of a specific Okta Group
get_user
Input takes the explicit Okta User ID string. Get detailed profile and state for a specific Okta user
list_apps
Identifies available sign-on integrations spanning raw OIDC, classical SAML 2.0, SCIM provisioning connections, and SWA (Secure Web Authentication) apps. List all applications integrated within the Okta dashboard
list_group_users
Essential when determining precisely who was automatically granted SCIM or cloud application licenses due to their directory membership mapping. List all users currently assigned to an Okta Group
list_groups
Group policies explicitly determine which users can authenticate into which bound SAML apps, making this endpoint critical for auditing permissions. List all security, app, and dynamic Okta Groups
list_system_logs
Contains every discrete sign-in attempt, MFA challenge result, configuration tweak, and malicious password spraying anomaly. Max 100 recent entries. Retrieve Recent Okta System and Audit log events
list_users
Used for organization-wide identity reporting. List all users configured in the Okta Universal Directory
Example Prompts for Okta in Cline
Ready-to-use prompts you can give your Cline agent to start working with Okta immediately.
"Retrieve the user profile for 'mark@example.com'."
"Clear all active sessions for user 'mike@example.com' immediately."
"List all active application mappings for the 'Contractors' group."
Troubleshooting Okta MCP Server with Cline
Common issues when connecting Okta to Cline through the Vinkius, and how to resolve them.
Server shows error in sidebar
Okta + Cline FAQ
Common questions about integrating Okta MCP Server with Cline.
How does Cline connect to MCP servers?
Can Cline run MCP tools without approval?
Does Cline support multiple MCP servers at once?
Connect Okta with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Okta to Cline
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
