Ping Identity MCP Server for Cline 10 tools — connect in under 2 minutes
Cline is an autonomous AI coding agent inside VS Code that plans, executes, and iterates on tasks. Wire Ping Identity through Vinkius and Cline gains direct access to every tool. from data retrieval to workflow automation. without leaving the terminal.
ASK AI ABOUT THIS MCP SERVER
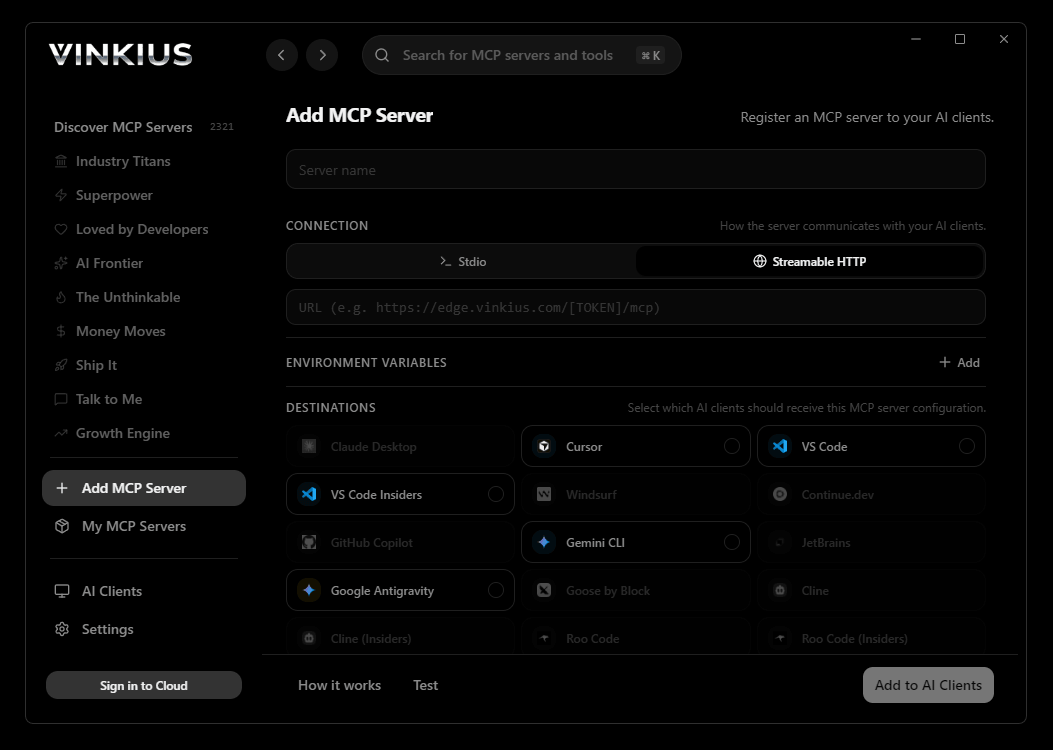
Vinkius supports streamable HTTP and SSE.
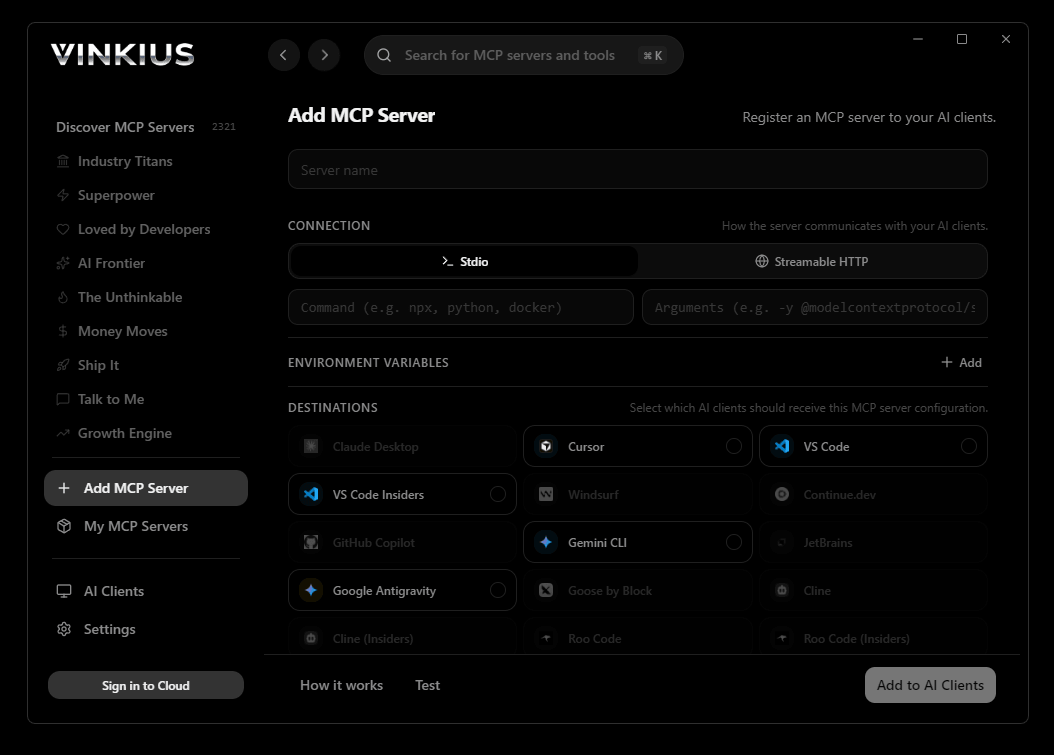
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Ping Identity and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"ping-identity": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Ping Identity MCP Server
Connect your Ping Identity environment to any AI agent to streamline identity and access management (IAM). You can audit users, check security policies, and review applications directly through conversation.
Cline operates autonomously inside VS Code. it reads your codebase, plans a strategy, and executes multi-step tasks including Ping Identity tool calls without waiting for prompts between steps. Connect 10 tools through Vinkius and Cline can fetch data, generate code, and commit changes in a single autonomous run.
What you can do
- User Management — List identities, view detailed user profiles, and safely delete users across the enterprise directory.
- Applications & Groups — Audit all Web, Native, or SPA apps federated under your environment, and list active IAM groups.
- Populations — Review isolated populations dividing contractors, partners, or B2B clients.
- Risk & Policies — Inspect active Risk Management rules and Zero-Trust sign-on workflows dictating real-time MFA.
The Ping Identity MCP Server exposes 10 tools through the Vinkius. Connect it to Cline in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Ping Identity to Cline via MCP
Follow these steps to integrate the Ping Identity MCP Server with Cline.
Open Cline MCP Settings
Click the MCP Servers icon in the Cline sidebar panel
Add remote server
Click "Add MCP Server" and paste the configuration above
Enable the server
Toggle the server switch to ON
Start using Ping Identity
Ask Cline: "Using Ping Identity, help me...". 10 tools available
Why Use Cline with the Ping Identity MCP Server
Cline provides unique advantages when paired with Ping Identity through the Model Context Protocol.
Cline operates autonomously. it reads your codebase, plans a strategy, and executes multi-step tasks including MCP tool calls without step-by-step prompts
Runs inside VS Code, so you get MCP tool access alongside your existing extensions, terminal, and version control in a single window
Cline can create, edit, and delete files based on MCP tool responses, enabling end-to-end automation from data retrieval to code generation
Transparent execution: every tool call and file change is shown in Cline's activity log for full visibility and approval before committing
Ping Identity + Cline Use Cases
Practical scenarios where Cline combined with the Ping Identity MCP Server delivers measurable value.
Autonomous feature building: tell Cline to fetch data from Ping Identity and scaffold a complete module with types, handlers, and tests
Codebase refactoring: use Ping Identity tools to validate live data while Cline restructures your code to match updated schemas
Automated testing: Cline fetches real responses from Ping Identity and generates snapshot tests or mocks based on actual payloads
Incident response: query Ping Identity for real-time status and let Cline generate hotfix patches based on the findings
Ping Identity MCP Tools for Cline (10)
These 10 tools become available when you connect Ping Identity to Cline via MCP:
delete_user
Revokes all current session tokens, nullifies application scopes, isolates SCIM directory references, and executes the formal deletion API. Hard delete a user identity and purge related credentials
get_application
Determines configured Implicit/Authorization Code grants, token lifespan definitions, embedded sign-on policies, and allowed callback URIs required for stringent redirection security mapping. Get configuration for a single federated Ping Identity application
get_group
View explicit details encompassing a standard Ping Group
get_user
Get complete contextual metadata for a specific Ping Identity user
list_applications
Crucial to verify application exposure footprint. List Web, Native or SPA apps federated under standard PingOne
list_groups
Allows mapping high-level RBAC scopes dynamically injected into ID tokens returned via SSO channels upon successful client authorization flows. List identity Groups utilized for aggregate permissions
list_populations
g., 'Contractors', 'Partners', 'B2B Clients') possessing inherently different default password complexities, independent password expiration parameters, and isolated self-service recovery scopes. List isolated Populations logically partitioning the Environment
list_risk_policies
Evaluates contextual IP anomalies, impossible travel, blocklisted VPN routes, or behavioral irregularities explicitly stepping up authentication flows or directly blocking malicious login execution. List active Risk Management rules dictating real-time MFA
list_sign_on_policies
Sign-on policies chain distinct rules together enforcing explicit MFA prompts, enforcing complex password structures based on population assignment, or mandating implicit biometric validation prior to releasing environment tokens. List logical Sign-on flows and strict authentication conditions
list_users
Paginates across all bounded external and internal localized users containing primary credentials, deeply nested JSON identifiers, and physical verification states assigned under the Enterprise Directory schema. List all user identities within the standard PingOne Environment
Example Prompts for Ping Identity in Cline
Ready-to-use prompts you can give your Cline agent to start working with Ping Identity immediately.
"Can you list all OIDC applications configured in PingOne and highlight any insecure callbacks?"
"Provide the active list of Zero-Trust risk policies governing my environment."
"Delete the specific suspended user profile assigned to the ID `81773-XYZ-192`."
Troubleshooting Ping Identity MCP Server with Cline
Common issues when connecting Ping Identity to Cline through the Vinkius, and how to resolve them.
Server shows error in sidebar
Ping Identity + Cline FAQ
Common questions about integrating Ping Identity MCP Server with Cline.
How does Cline connect to MCP servers?
Can Cline run MCP tools without approval?
Does Cline support multiple MCP servers at once?
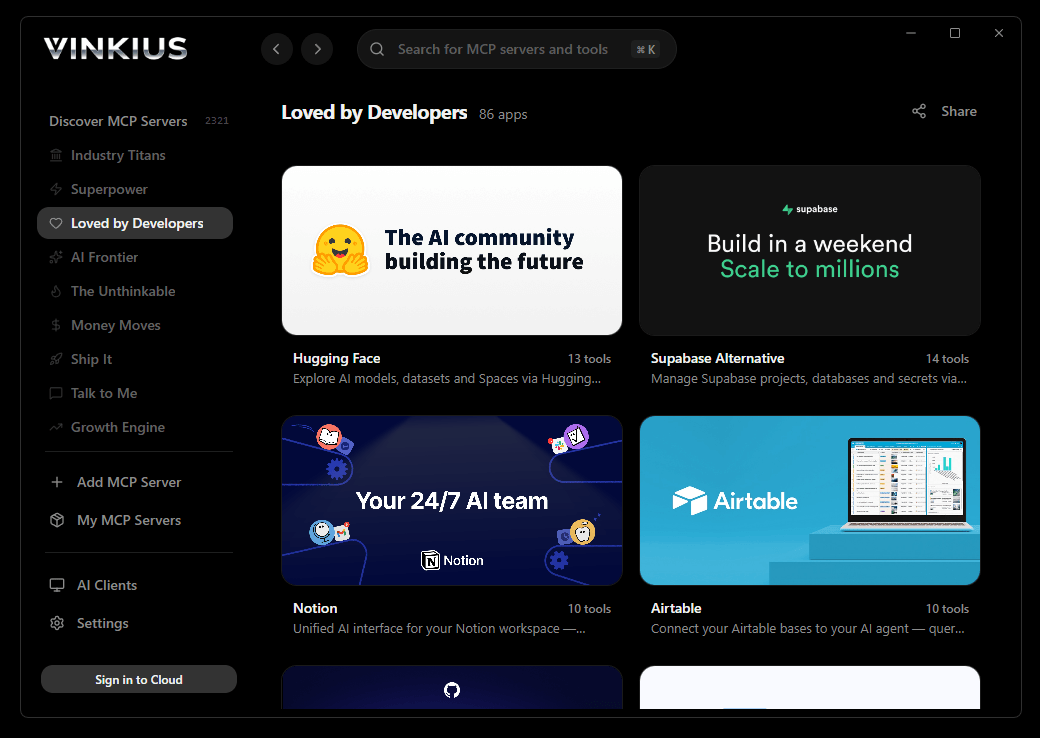
Connect Ping Identity with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Ping Identity to Cline
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
