Runlayer MCP Server for Cline 27 tools — connect in under 2 minutes
Cline is an autonomous AI coding agent inside VS Code that plans, executes, and iterates on tasks. Wire Runlayer through the Vinkius and Cline gains direct access to every tool — from data retrieval to workflow automation — without leaving the terminal.
ASK AI ABOUT THIS MCP SERVER
Vinkius supports streamable HTTP and SSE.
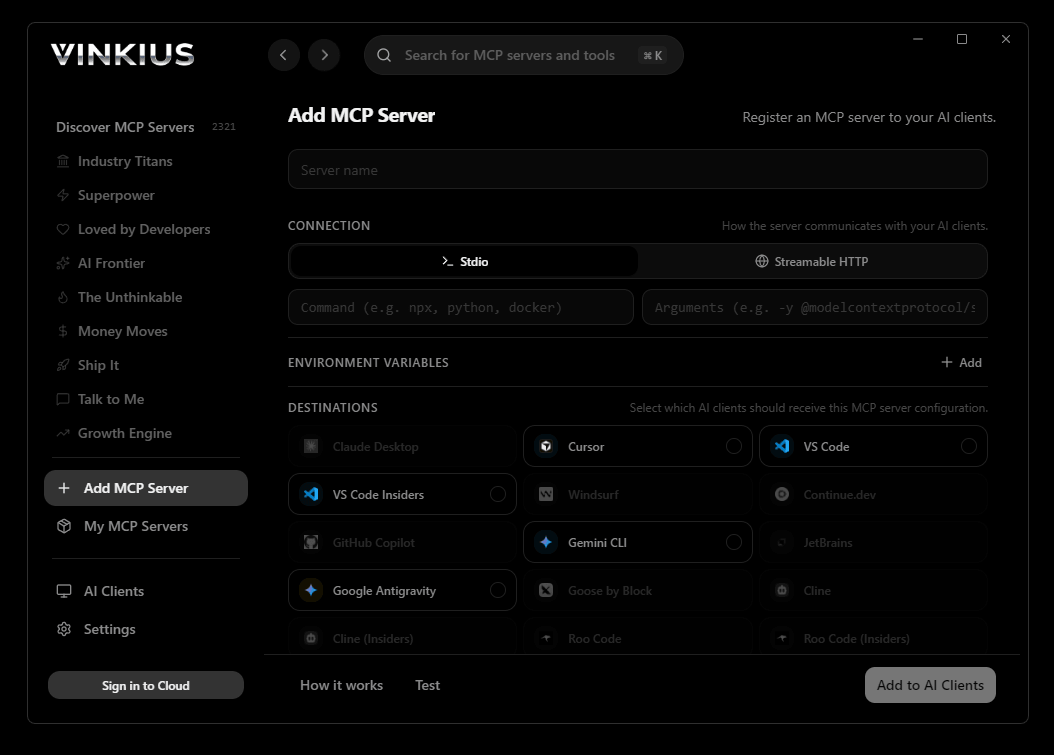
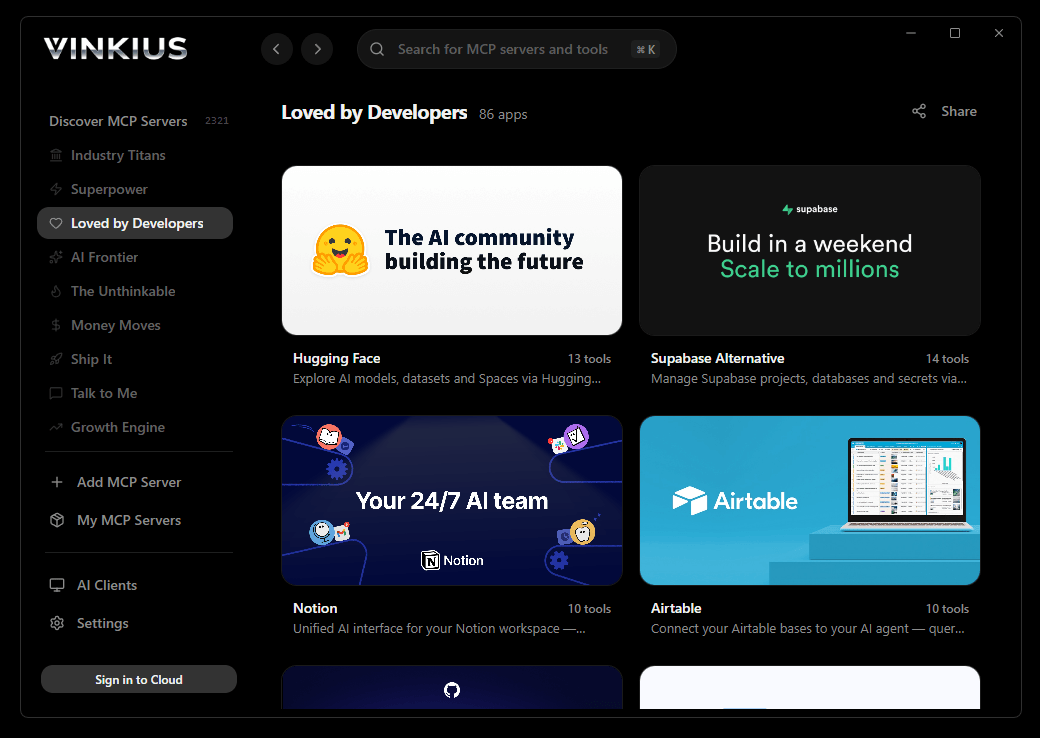
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Runlayer and 2,500+ MCP Servers from a single visual interface.

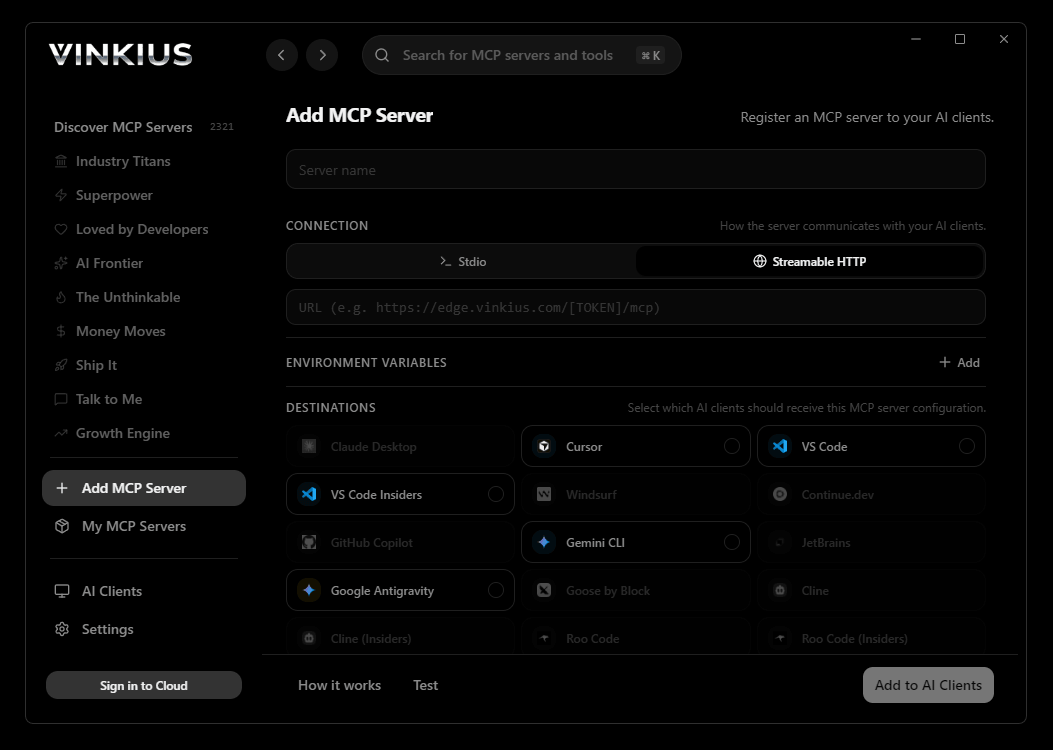
{
"mcpServers": {
"runlayer": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Runlayer MCP Server
What you can do
Connect AI agents to the Runlayer Enterprise Control Plane for comprehensive MCP ecosystem management:
Cline operates autonomously inside VS Code — it reads your codebase, plans a strategy, and executes multi-step tasks including Runlayer tool calls without waiting for prompts between steps. Connect 27 tools through the Vinkius and Cline can fetch data, generate code, and commit changes in a single autonomous run.
- Manage MCP Servers — register, inspect, update, and remove serverless MCP endpoints
- Manage Skills — create, assign, and version reusable agent capabilities
- Manage Agents — onboard AI agents (Claude, Cursor, VS Code, custom) with proper security guardrails
- Enforce Policies — define and audit security policies governing MCP access and agent permissions
- Audit Everything — retrieve complete audit trails of all MCP, skill, agent, and policy operations
- Manage API Keys — create, rotate, and revoke organization and personal API keys
- Run Security Scans — discover shadow AI, unauthorized MCP servers, and policy violations across your organization
- Monitor Organization Health — review member activity, server inventory, and security posture
The Runlayer MCP Server exposes 27 tools through the Vinkius. Connect it to Cline in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Runlayer to Cline via MCP
Follow these steps to integrate the Runlayer MCP Server with Cline.
Open Cline MCP Settings
Click the MCP Servers icon in the Cline sidebar panel
Add remote server
Click "Add MCP Server" and paste the configuration above
Enable the server
Toggle the server switch to ON
Start using Runlayer
Ask Cline: "Using Runlayer, help me..." — 27 tools available
Why Use Cline with the Runlayer MCP Server
Cline provides unique advantages when paired with Runlayer through the Model Context Protocol.
Cline operates autonomously — it reads your codebase, plans a strategy, and executes multi-step tasks including MCP tool calls without step-by-step prompts
Runs inside VS Code, so you get MCP tool access alongside your existing extensions, terminal, and version control in a single window
Cline can create, edit, and delete files based on MCP tool responses, enabling end-to-end automation from data retrieval to code generation
Transparent execution: every tool call and file change is shown in Cline's activity log for full visibility and approval before committing
Runlayer + Cline Use Cases
Practical scenarios where Cline combined with the Runlayer MCP Server delivers measurable value.
Autonomous feature building: tell Cline to fetch data from Runlayer and scaffold a complete module with types, handlers, and tests
Codebase refactoring: use Runlayer tools to validate live data while Cline restructures your code to match updated schemas
Automated testing: Cline fetches real responses from Runlayer and generates snapshot tests or mocks based on actual payloads
Incident response: query Runlayer for real-time status and let Cline generate hotfix patches based on the findings
Runlayer MCP Tools for Cline (27)
These 27 tools become available when you connect Runlayer to Cline via MCP:
create_agent
Requires agent name and type (claude_desktop, cursor, vs_code, custom). Optionally assign MCP servers, skills, and policies during registration. Returns the created agent details. Use this to onboard new AI agents to your enterprise control plane with proper security guardrails. Register a new AI agent in Runlayer
create_api_key
Returns the key value (shown only once) and metadata. Use this to create keys for integrations, CI/CD pipelines, or service accounts. Store the key value securely immediately after creation. Create a new API key for your Runlayer organization
create_mcp_server
Requires server name and connection details (URL, authentication method). Optionally assign skills, agents, and policies during registration. Returns the created server details including the new UUID. Use this to onboard new MCP servers to your enterprise control plane. Register a new MCP server in Runlayer
create_policy
Requires policy name and rule definitions. Returns the created policy. Use this to enforce security standards, restrict access to sensitive MCP servers, or define audit requirements. Create a new security or access policy in Runlayer
create_skill
Requires skill name and description. Optionally define input/output schemas and initial MCP server assignments. Returns the created skill details. Use this to codify reusable agent capabilities for consistent use across your organization. Register a new skill (agent capability) in Runlayer
delete_agent
This disconnects the agent from all MCP servers and removes policy assignments. Requires the agent ID. Confirm with the user before proceeding. Remove an AI agent from Runlayer
delete_mcp_server
This action disconnects all associated agents and removes policy assignments. Requires the server UUID. Confirm with the user before proceeding. Remove an MCP server from Runlayer
delete_policy
All resources previously governed by this policy will no longer be subject to its rules. Requires the policy ID. Confirm with the user before proceeding. Remove a security or access policy from Runlayer
delete_skill
Does not delete the underlying MCP server tools. Requires the skill ID. Confirm with the user before proceeding. Remove a skill from Runlayer
get_agent
Requires the agent ID from list_agents results. Use this to review agent configuration, audit access patterns, or troubleshoot connectivity. Get detailed information about a specific AI agent
get_audit_logs
Returns timestamps, actor identities, action types, affected resources, and outcomes. Use this for compliance reporting, security investigations, or operational troubleshooting. Get audit logs for your Runlayer organization
get_mcp_server
Requires the server UUID from list_mcp_servers results. Use this to review server configuration, verify security compliance, or troubleshoot connectivity issues. Get detailed information about a specific MCP server
get_organization
Use this to verify your organization configuration or get an overview of your MCP ecosystem. Get your Runlayer organization details
get_scan_results
Requires the scan ID from run_mcp_sweep_scan results. Use this to review shadow AI discoveries, identify policy violations, or generate compliance reports. Get results from an MCP sweep scan
get_skill
Requires the skill ID from list_skills results. Use this to review skill configuration or understand capability dependencies. Get detailed information about a specific skill
list_agents
Returns agent names, IDs, types (Claude Desktop, Cursor, custom), assigned MCP servers, active skills, policy compliance status, and last activity timestamps. Use this to understand your agent ecosystem and verify which agents have access to which MCP servers. List all AI agents registered in your Runlayer organization
list_api_keys
Use this to audit key inventory, identify unused keys, or prepare for key rotation. List all API keys for your Runlayer organization
list_mcp_servers
Returns server names, UUIDs, status (active, inactive, blocked), assigned skills, connected agents, policy associations, and last activity timestamps. Use this as the first step to understand your MCP server inventory before managing individual servers, applying policies, or reviewing security posture. List all registered MCP servers in your Runlayer organization
list_members
Use this to audit access, review role assignments, or identify inactive accounts. List all members of your Runlayer organization
list_policies
Returns policy names, descriptions, enforcement status, affected resources, and violation counts. Use this to review your security posture before creating or modifying policies. List all security and access policies in your Runlayer organization
list_skills
Returns skill names, descriptions, associated MCP servers, usage counts, and version information. Use this to discover available capabilities before assigning them to agents or MCP servers. List all skills registered in your Runlayer organization
revoke_api_key
This action cannot be undone. Requires the key ID. Use this for compromised keys, unused keys, or during security incidents. Revoke an API key immediately
run_mcp_sweep_scan
Returns a scan ID which can be used with get_scan_results to retrieve findings. Use this for security assessments, compliance audits, or shadow AI detection. Run an MCP sweep scan to discover shadow AI across your organization
update_agent
Only pass the fields you want to change. Requires the agent ID. Use this to update agent assignments or modify metadata. Update an existing AI agent configuration
update_mcp_server
Only pass the fields you want to change. Requires the server UUID. Use this to update server endpoints, rotate credentials, or modify policy assignments. Update an existing MCP server configuration
update_policy
Only pass the fields you want to change. Requires the policy ID. Use this to refine security requirements, update access controls, or modify audit rules. Update an existing security or access policy
update_skill
Only pass the fields you want to change. Requires the skill ID. Use this to refine skill definitions or update documentation. Update an existing skill configuration
Example Prompts for Runlayer in Cline
Ready-to-use prompts you can give your Cline agent to start working with Runlayer immediately.
"Show me all MCP servers registered in our organization and their security status"
"Run a shadow AI discovery scan across our organization and show me the findings"
"Create a new policy that restricts MCP server access to only approved developers"
Troubleshooting Runlayer MCP Server with Cline
Common issues when connecting Runlayer to Cline through the Vinkius, and how to resolve them.
Server shows error in sidebar
Runlayer + Cline FAQ
Common questions about integrating Runlayer MCP Server with Cline.
How does Cline connect to MCP servers?
Can Cline run MCP tools without approval?
Does Cline support multiple MCP servers at once?
Connect Runlayer with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Runlayer to Cline
Get your token, paste the configuration, and start using 27 tools in under 2 minutes. No API key management needed.
