SecurityTrails MCP Server for Claude Code 10 tools — connect in under 2 minutes
Claude Code is Anthropic's agentic CLI for terminal-first development. Add SecurityTrails as an MCP server in one command and Claude Code will discover every tool at runtime. ideal for automation pipelines, CI/CD integration, and headless workflows via Vinkius.
ASK AI ABOUT THIS MCP SERVER
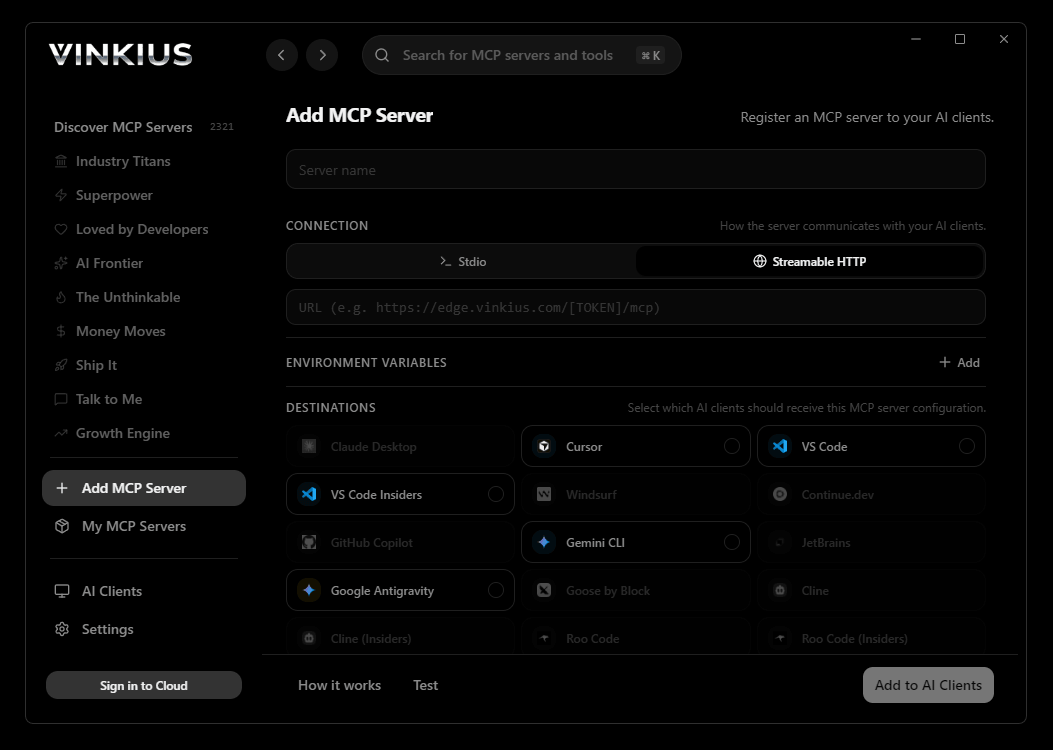
Vinkius supports streamable HTTP and SSE.
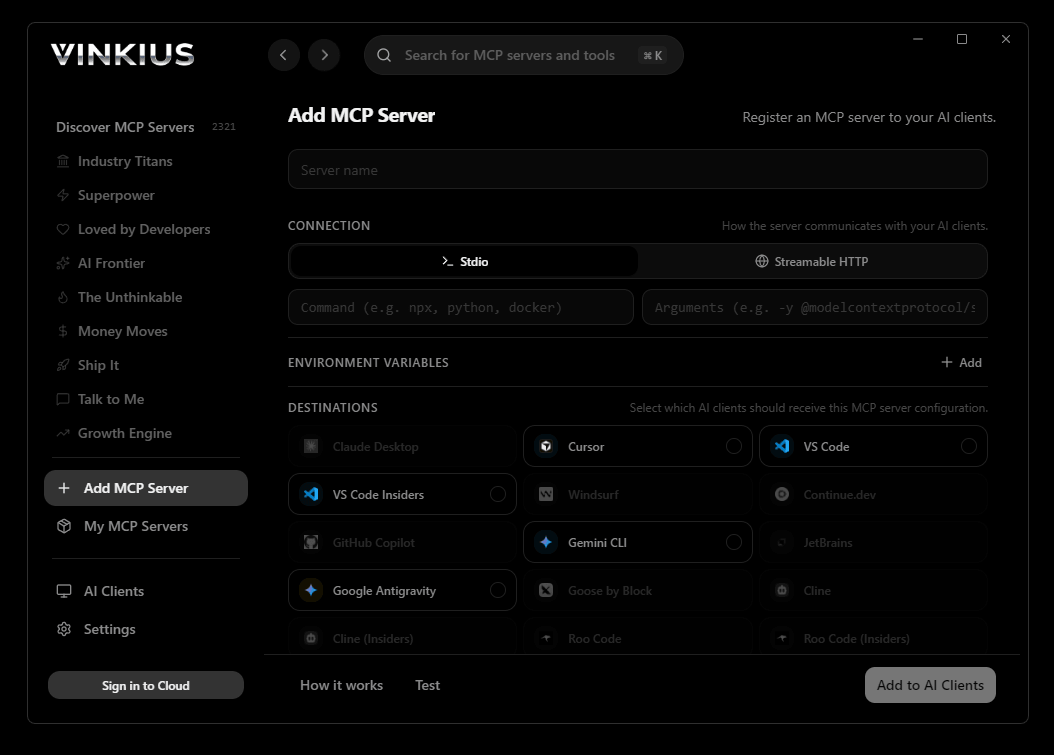
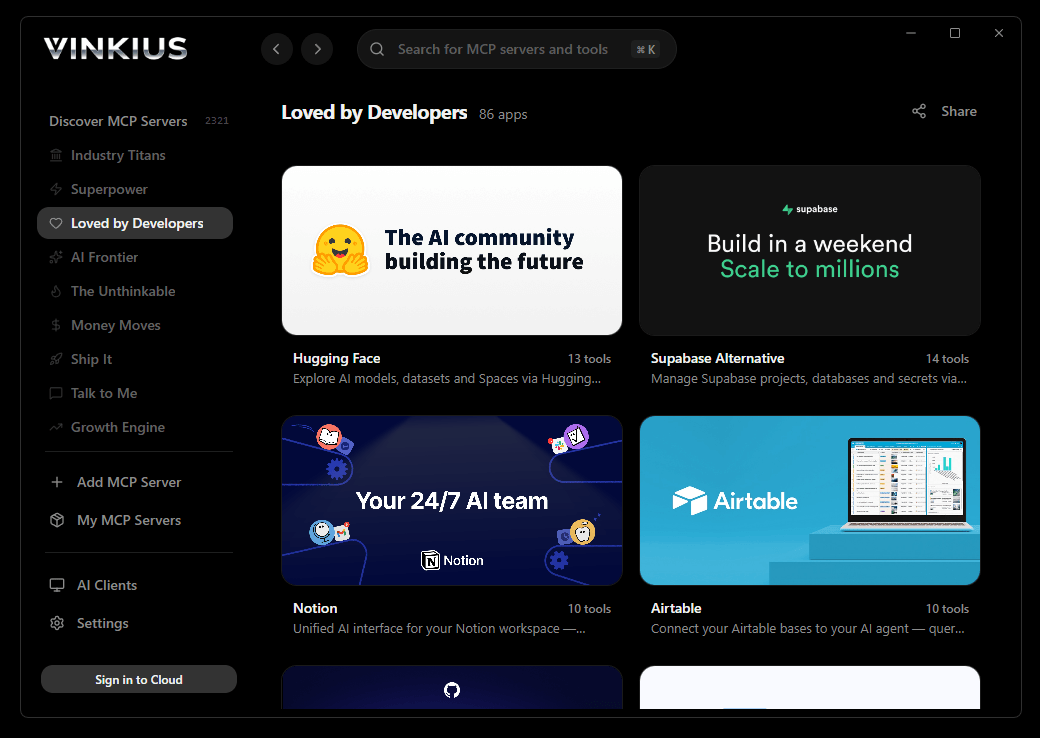
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install SecurityTrails and 2,500+ MCP Servers from a single visual interface.

# Your Vinkius token. get it at cloud.vinkius.com
claude mcp add securitytrails --transport http "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About SecurityTrails MCP Server
Connect your SecurityTrails account to any AI agent and empower your OSINT, bug bounty, and threat intelligence workflows with the world's most comprehensive domain and IP database.
Claude Code registers SecurityTrails as an MCP server in a single terminal command. Once connected, Claude Code discovers all 10 tools at runtime and can call them headlessly. ideal for CI/CD pipelines, cron jobs, and automated workflows where SecurityTrails data drives decisions without human intervention.
What you can do
- Attack Surface Mapping — Instantly enumerate all subdomains for any target organization to map their external footprint
- Historical DNS Analysis — Look back in time at DNS records (A, MX, NS, TXT) to find hidden infrastructure, bypassed firewalls, or legacy systems
- Reverse IP Lookups — Find all domains hosted on a specific IP address to identify shared hosting or related corporate assets
- Advanced Threat Hunting — Use the SecurityTrails DSL (Domain Specific Language) to query the entire internet for specific tech stacks or vulnerable infrastructure
- Ownership Intelligence — Access current and historical WHOIS records to track domain ownership changes and unmask hidden threat actors
- Corporate Associations — Discover domains strongly associated with your primary target to expand your investigation scope
The SecurityTrails MCP Server exposes 10 tools through the Vinkius. Connect it to Claude Code in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect SecurityTrails to Claude Code via MCP
Follow these steps to integrate the SecurityTrails MCP Server with Claude Code.
Install Claude Code
Run npm install -g @anthropic-ai/claude-code if not already installed
Add the MCP Server
Run the command above in your terminal
Verify the connection
Run claude mcp to list connected servers, or type /mcp inside a session
Start using SecurityTrails
Ask Claude: "Using SecurityTrails, show me...". 10 tools are ready
Why Use Claude Code with the SecurityTrails MCP Server
Claude Code provides unique advantages when paired with SecurityTrails through the Model Context Protocol.
Single-command setup: `claude mcp add` registers the server instantly. no config files to edit or applications to restart
Terminal-native workflow means MCP tools integrate seamlessly into shell scripts, CI/CD pipelines, and automated DevOps tasks
Claude Code runs headlessly, enabling unattended batch processing using SecurityTrails tools in cron jobs or deployment scripts
Built by the same team that created the MCP protocol, ensuring first-class compatibility and the fastest adoption of new protocol features
SecurityTrails + Claude Code Use Cases
Practical scenarios where Claude Code combined with the SecurityTrails MCP Server delivers measurable value.
CI/CD integration: embed SecurityTrails tool calls in your deployment pipeline to validate configurations or fetch secrets before shipping
Headless batch processing: schedule Claude Code to query SecurityTrails nightly and generate reports without human intervention
Shell scripting: pipe SecurityTrails outputs into other CLI tools for data transformation, filtering, and aggregation
Infrastructure monitoring: run Claude Code in a cron job to query SecurityTrails status endpoints and alert on anomalies
SecurityTrails MCP Tools for Claude Code (10)
These 10 tools become available when you connect SecurityTrails to Claude Code via MCP:
get_api_usage
Check current SecurityTrails API quota usage
get_associated_domains
Great for expanding the scope of an investigation. Find other domains associated with a target domain
get_dns_history
Useful for finding old IPs that might still be hosting vulnerable software, or tracking infrastructure migration over time. Retrieve historical DNS records for a domain
get_domain_details
Essential for mapping out a target domain's existing infrastructure. Get complete domain intelligence and current DNS records
get_domain_tags
Get classification tags for a domain
get_domains_by_ip
Essential for understanding shared hosting environments or identifying hidden vhosts. Find all domains pointed to a specific IP address
get_subdomains
Critical for attack surface mapping and asset discovery. Returns both active and inactive subdomains. Discover all subdomains for a given domain
get_whois
Get current WHOIS information for a domain
get_whois_history
Useful for OSINT investigations to uncover historical owners before privacy protection was enabled. Retrieve historical WHOIS records for a domain
search_dsl
Examples: `ipv4="1.1.1.1" AND mx="alt1.aspmx.l.google.com"` or `whois_email="admin@example.com"`. Check SecurityTrails docs for full DSL syntax. Advanced search using SecurityTrails DSL
Example Prompts for SecurityTrails in Claude Code
Ready-to-use prompts you can give your Claude Code agent to start working with SecurityTrails immediately.
"Find all subdomains for tesla.com."
"Check the historical 'A' records for example.com. Were there any changes in 2021?"
"What domains are hosted on the IP 8.8.8.8?"
Troubleshooting SecurityTrails MCP Server with Claude Code
Common issues when connecting SecurityTrails to Claude Code through the Vinkius, and how to resolve them.
Command not found: claude
npm install -g @anthropic-ai/claude-codeConnection timeout
SecurityTrails + Claude Code FAQ
Common questions about integrating SecurityTrails MCP Server with Claude Code.
How do I add an MCP server to Claude Code?
claude mcp add --transport http "" in your terminal. Claude Code registers the server and discovers all tools immediately.Can Claude Code run MCP tools in headless mode?
How do I list all connected MCP servers?
claude mcp in your terminal to see all registered servers and their status, or type /mcp inside an active Claude Code session.Connect SecurityTrails with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect SecurityTrails to Claude Code
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
