Semgrep MCP Server for Windsurf 10 tools — connect in under 2 minutes
Windsurf brings agentic AI coding to a purpose-built IDE. Connect Semgrep through the Vinkius and Cascade will auto-discover every tool — ask questions, generate code, and act on live data without leaving your editor.
ASK AI ABOUT THIS MCP SERVER
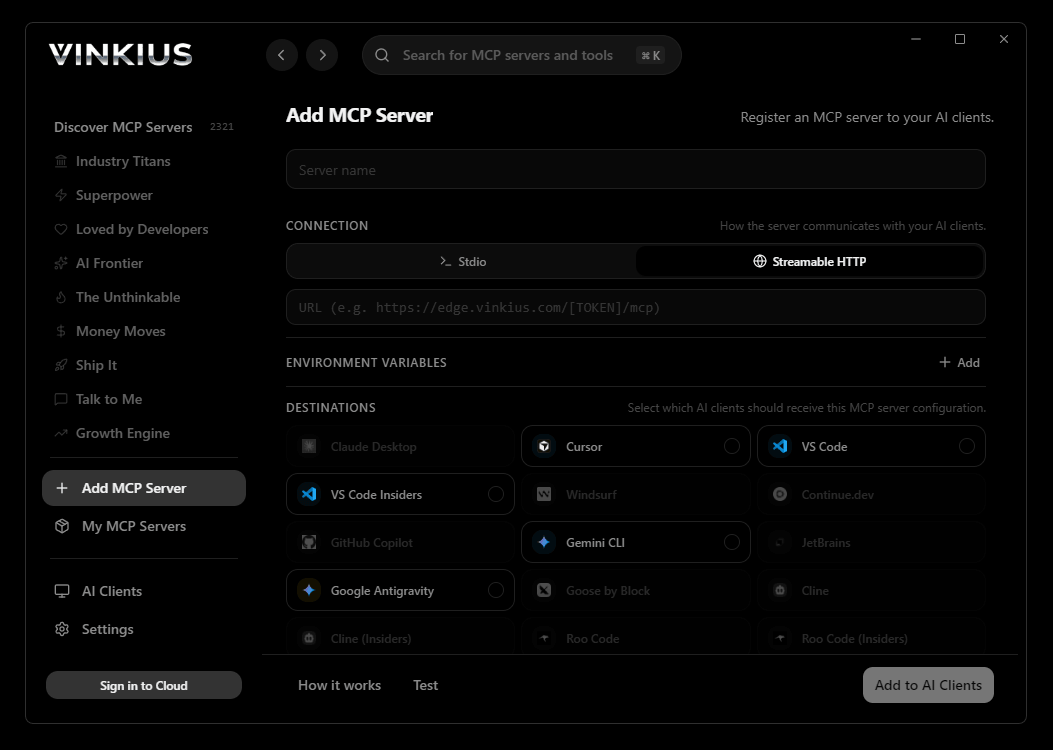
Vinkius supports streamable HTTP and SSE.
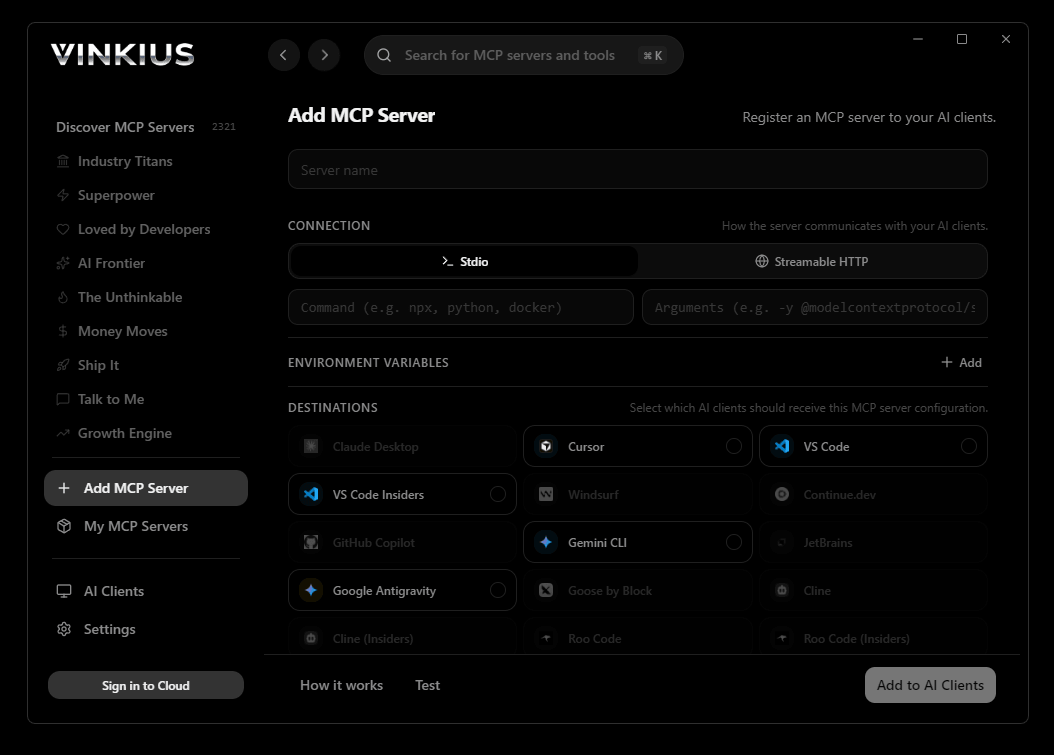
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Semgrep and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"semgrep": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Semgrep MCP Server
Connect the Semgrep AppSec platform directly to your AI agent to radically accelerate code security triaging. Instead of forcing developers to jump between their IDE and the Semgrep dashboard, empower your AI to pull 'Findings', analyze the vulnerable syntax, and instantly close false positives.
Windsurf's Cascade agent chains multiple Semgrep tool calls autonomously — query data, analyze results, and generate code in a single agentic session. Paste the Vinkius Edge URL, reload, and all 10 tools are immediately available. Real-time tool feedback appears inline, so you see API responses directly in your editor.
What you can do
- Triage Findings (Bugs) — Instruct the agent to grab the latest CI vulnerability findings and immediately push a status update to mark it as fixed, ignored, or mitigated (
update_finding_status) - Rule Management — Request the AI to look at a newly discovered bad coding pattern and command it to write and deploy a matching custom semantic rule (
create_rule) to your organizational deployment - Project & Deployment Scoping — Map out all repositories running Semgrep actions and check their overarching security health scores in milliseconds
- Comprehensive Forensics — Fetch granular SCA and SAST semantic flaw definitions, including exact snippets, CVE links, and the specific bad lines causing the trigger
The Semgrep MCP Server exposes 10 tools through the Vinkius. Connect it to Windsurf in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Semgrep to Windsurf via MCP
Follow these steps to integrate the Semgrep MCP Server with Windsurf.
Open MCP Settings
Go to Settings → MCP Configuration or press Cmd+Shift+P and search "MCP"
Add the server
Paste the JSON configuration above into mcp_config.json
Save and reload
Windsurf will detect the new server automatically
Start using Semgrep
Open Cascade and ask: "Using Semgrep, help me..." — 10 tools available
Why Use Windsurf with the Semgrep MCP Server
Windsurf provides unique advantages when paired with Semgrep through the Model Context Protocol.
Windsurf's Cascade agent autonomously chains multiple tool calls in sequence, solving complex multi-step tasks without manual intervention
Purpose-built for agentic workflows — Cascade understands context across your entire codebase and integrates MCP tools natively
JSON-based configuration means zero code changes: paste a URL, reload, and all 10 tools are immediately available
Real-time tool feedback is displayed inline, so you see API responses directly in your editor without switching contexts
Semgrep + Windsurf Use Cases
Practical scenarios where Windsurf combined with the Semgrep MCP Server delivers measurable value.
Automated code generation: ask Cascade to fetch data from Semgrep and generate models, types, or handlers based on real API responses
Live debugging: query Semgrep tools mid-session to inspect production data while debugging without leaving the editor
Documentation generation: pull schema information from Semgrep and have Cascade generate comprehensive API docs automatically
Rapid prototyping: combine Semgrep data with Cascade's code generation to scaffold entire features in minutes
Semgrep MCP Tools for Windsurf (10)
These 10 tools become available when you connect Semgrep to Windsurf via MCP:
create_rule
Allows developers to forbid project-specific bad patterns securely and continuously across the enterprise repositories. Create a customized Semgrep security rule within the platform
delete_rule
Delete a custom Semgrep security rule from the deployment
get_finding_details
Explains the exact malicious code block, suggests semantic fixes, states whether it is blocking PRs in CI, and links to CVE data (if an SCA supply chain defect). Get atomic details for a specific Semgrep flaw
get_metrics
Typically consumed to render executive security dashboards. Get AppSec metrics and compliance stats for Semgrep
get_project
Search for a precise Semgrep project by exact repository name
list_deployments
The primary key is the deployment slug identifier. Almost all subsequent API operations targeting rules, projects, or findings will require this deployment slug to define the scope. List Semgrep organizational deployments
list_findings
Findings provide snippet details, file line numbers, severity, and rule types. Fetch global static analysis security findings for a deployment
list_projects
Projects maintain a link between developers and static security scan outputs over time. List Semgrep projects (repositories) monitored in a deployment
list_rules
The rules are structured YAML definitions that search for semantic anti-patterns in codebases (e.g., unparameterized SQL queries, hardcoded AWS keys). List Semgrep semantic rules deployed globally
update_finding_status
Valid states generally include active, fixed, false_positive, ignored, mitigated. Resolving findings through this API cleans up the developer experience when managing compliance queues. Mark a Semgrep finding state (e.g., fixed, false positive)
Example Prompts for Semgrep in Windsurf
Ready-to-use prompts you can give your Windsurf agent to start working with Semgrep immediately.
"List the most severe unmitigated findings currently breaking our CI/CD pipeline on the 'vinkius/cloud' repository."
"Mark vulnerability issue ID #58032 as a 'false_positive' using the update finding tool."
"Review the company's Semgrep performance metrics focusing on fix rate."
Troubleshooting Semgrep MCP Server with Windsurf
Common issues when connecting Semgrep to Windsurf through the Vinkius, and how to resolve them.
Server not connecting
Semgrep + Windsurf FAQ
Common questions about integrating Semgrep MCP Server with Windsurf.
How does Windsurf discover MCP tools?
mcp_config.json file on startup and connects to each configured server via Streamable HTTP. Tools are listed in the MCP panel and available to Cascade automatically.Can Cascade chain multiple MCP tool calls?
Does Windsurf support multiple MCP servers?
mcp_config.json. Each server's tools appear in the MCP panel and Cascade can use tools from different servers in a single flow.Connect Semgrep with your favorite client
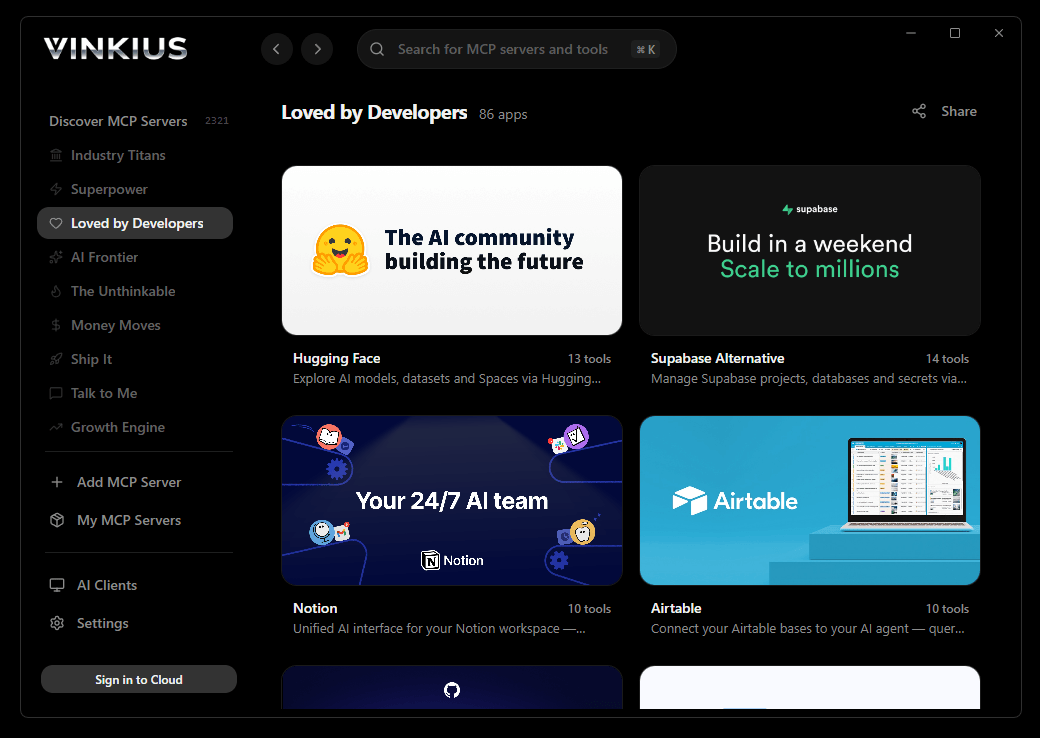
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Semgrep to Windsurf
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
