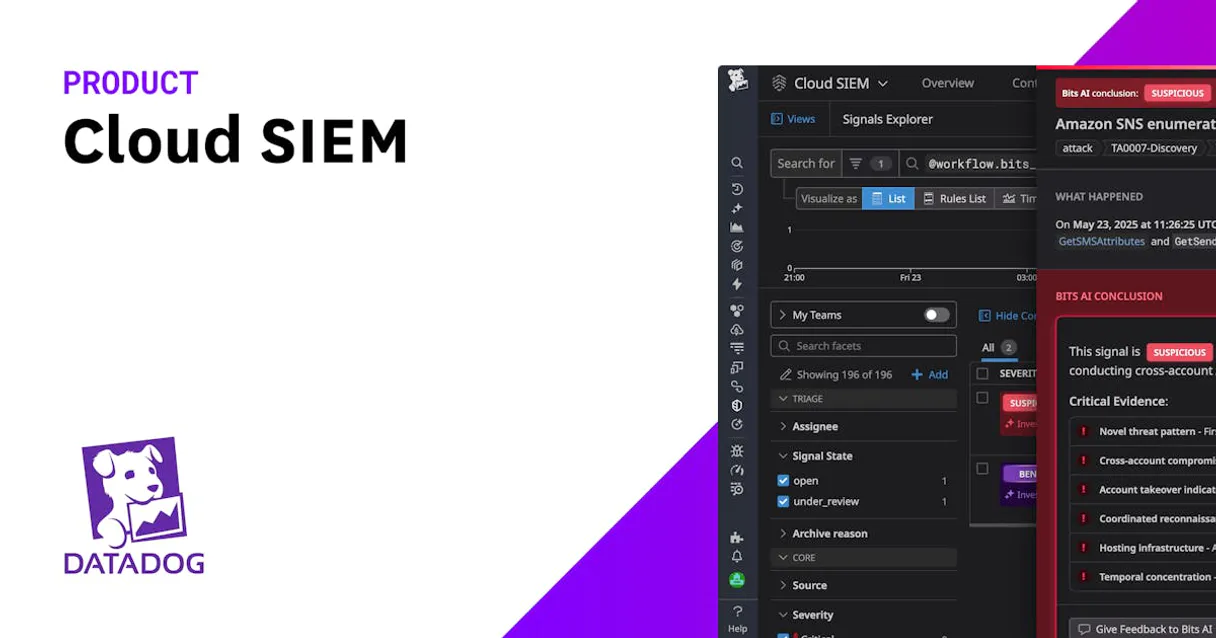
Datadog Cloud SIEM MCP Server for Cline 10 tools — connect in under 2 minutes
Cline is an autonomous AI coding agent inside VS Code that plans, executes, and iterates on tasks. Wire Datadog Cloud SIEM through the Vinkius and Cline gains direct access to every tool — from data retrieval to workflow automation — without leaving the terminal.
ASK AI ABOUT THIS MCP SERVER
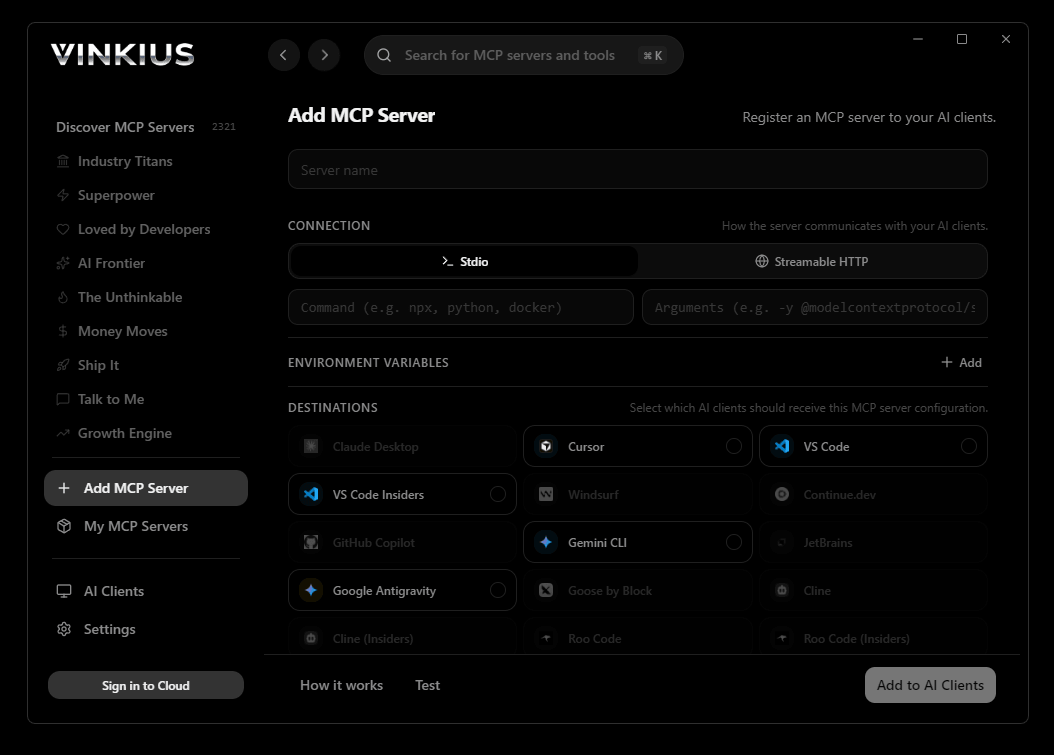
Vinkius supports streamable HTTP and SSE.
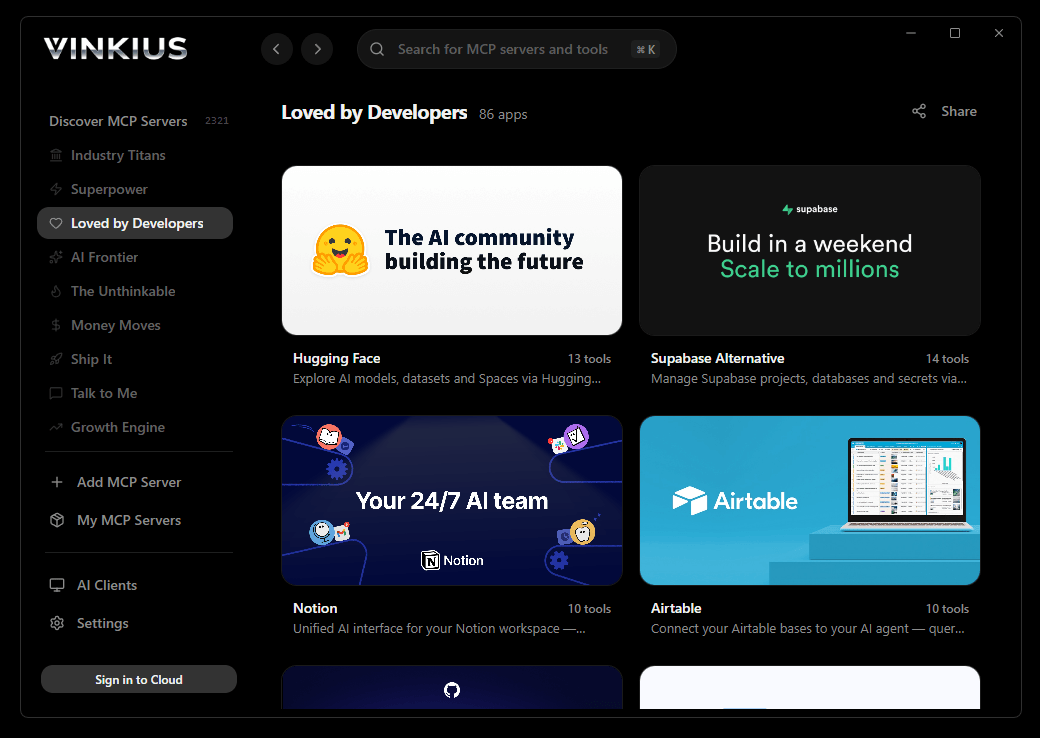
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Datadog Cloud SIEM and 2,500+ MCP Servers from a single visual interface.

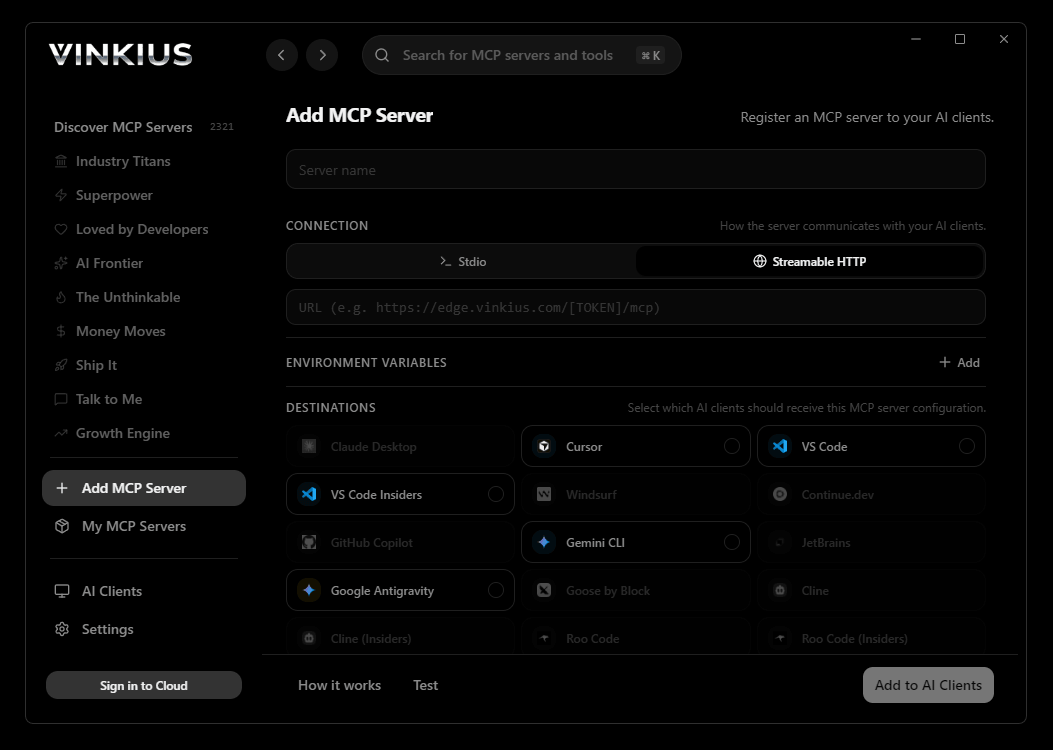
{
"mcpServers": {
"datadog-cloud-siem": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Datadog Cloud SIEM MCP Server
Connect your Datadog security module to any AI agent and take full control of your Cloud SIEM and threat hunting workflows through natural conversation.
Cline operates autonomously inside VS Code — it reads your codebase, plans a strategy, and executes multi-step tasks including Datadog Cloud SIEM tool calls without waiting for prompts between steps. Connect 10 tools through the Vinkius and Cline can fetch data, generate code, and commit changes in a single autonomous run.
What you can do
- Security Signal Search — Execute ingestion searches returning critical threats detected by Datadog SIEM, CSPM, and CWS matching MITRE ATT&CK vectors
- Signal Triaging — Update the state of active threat alerts, transitioning signals from open to archived with audited false-positive justifications
- Detection Rule Management — List and retrieve exact logic for security rules identifying AWS CloudTrail deviations or Kubernetes root escalations
- Rule Orchestration — Construct new Cloud SIEM Log Detection rules by pushing raw name/message fields and specific Lucene query bindings
- Threat Hunting — Directly query raw Datadog logs with a 10s lookbehind to capture highly localized context matching malicious source IPs
- Security Filter Auditing — Retrieve global exclusion policies mapping to SIEM log pipelines to verify which low-value vectors are blocked
The Datadog Cloud SIEM MCP Server exposes 10 tools through the Vinkius. Connect it to Cline in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Datadog Cloud SIEM to Cline via MCP
Follow these steps to integrate the Datadog Cloud SIEM MCP Server with Cline.
Open Cline MCP Settings
Click the MCP Servers icon in the Cline sidebar panel
Add remote server
Click "Add MCP Server" and paste the configuration above
Enable the server
Toggle the server switch to ON
Start using Datadog Cloud SIEM
Ask Cline: "Using Datadog Cloud SIEM, help me..." — 10 tools available
Why Use Cline with the Datadog Cloud SIEM MCP Server
Cline provides unique advantages when paired with Datadog Cloud SIEM through the Model Context Protocol.
Cline operates autonomously — it reads your codebase, plans a strategy, and executes multi-step tasks including MCP tool calls without step-by-step prompts
Runs inside VS Code, so you get MCP tool access alongside your existing extensions, terminal, and version control in a single window
Cline can create, edit, and delete files based on MCP tool responses, enabling end-to-end automation from data retrieval to code generation
Transparent execution: every tool call and file change is shown in Cline's activity log for full visibility and approval before committing
Datadog Cloud SIEM + Cline Use Cases
Practical scenarios where Cline combined with the Datadog Cloud SIEM MCP Server delivers measurable value.
Autonomous feature building: tell Cline to fetch data from Datadog Cloud SIEM and scaffold a complete module with types, handlers, and tests
Codebase refactoring: use Datadog Cloud SIEM tools to validate live data while Cline restructures your code to match updated schemas
Automated testing: Cline fetches real responses from Datadog Cloud SIEM and generates snapshot tests or mocks based on actual payloads
Incident response: query Datadog Cloud SIEM for real-time status and let Cline generate hotfix patches based on the findings
Datadog Cloud SIEM MCP Tools for Cline (10)
These 10 tools become available when you connect Datadog Cloud SIEM to Cline via MCP:
create_detection_rule
Accepts raw name/message fields, specific Lucene query bindings filtering for malicious activity, and severity levels (info, low, medium, high, critical). Auto-activates upon creation. Construct a new Cloud SIEM Log Detection Rule
delete_detection_rule
Irreversible action. Pre-packaged rules provided by Datadog typically cannot be outright deleted (only disabled), making this primarily for user-created custom JSON rules. Permanently delete a Datadog Security Detection Rule
get_detection_rule
g. > 5 occurrences in 5 mins), severity bindings, tagging matrices, and Notification routing hooks tying into PagerDuty or Slack. Retrieve the exact logic/queries for a specific Detection Rule
get_raw_log_context
Use this immediately after verifying an attacker footprint. Additional threat hunt tool extracting exact log bounds (100 msgs)
list_detection_rules
Verifies the existence of proactive detections identifying AWS CloudTrail deviations, GCP anomalous IAM usage, and Kubernetes root escalations. List configured Datadog Security Detection Rules
list_security_filters
These filters inherently block high-volume, low-value logging vectors from ever reaching the SIEM evaluation engine in order to preserve compute budgets. List Security Filter configurations
search_raw_logs
Essential for rapid Threat Hunting before detection rules alert. Useful for extracting contextual VPC Flow Logs or application stack traces related to an active breach. Directly query raw Datadog Logs over the past 15/m for Threat Hunting
search_signals
Use lucene-based queries like "status:critical OR @usr.id:admin" to filter high severity indicators mapping to MITRE ATT&CK vectors. Search Cloud SIEM Security Signals (Alerts) over the last 24h
security_system_ping
Test API authentication validity against the Security Module
triage_signal
Transition signals directly from "open" to "archived", or from "archived" back to "open". If archiving, an official reason (e.g. "false_positive" or "testing_or_maintenance") must be assigned. Modify the state of a Datadog SIEM Security Signal
Example Prompts for Datadog Cloud SIEM in Cline
Ready-to-use prompts you can give your Cline agent to start working with Datadog Cloud SIEM immediately.
"List all critical security signals from the last 24h"
"Search logs for IP '1.2.3.4' to hunt for threats"
"Archive security signal 'sig_123' as a false positive"
Troubleshooting Datadog Cloud SIEM MCP Server with Cline
Common issues when connecting Datadog Cloud SIEM to Cline through the Vinkius, and how to resolve them.
Server shows error in sidebar
Datadog Cloud SIEM + Cline FAQ
Common questions about integrating Datadog Cloud SIEM MCP Server with Cline.
How does Cline connect to MCP servers?
Can Cline run MCP tools without approval?
Does Cline support multiple MCP servers at once?
Connect Datadog Cloud SIEM with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Datadog Cloud SIEM to Cline
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
