Honeywell Forge MCP Server for Cline 11 tools — connect in under 2 minutes
Cline is an autonomous AI coding agent inside VS Code that plans, executes, and iterates on tasks. Wire Honeywell Forge through Vinkius and Cline gains direct access to every tool. from data retrieval to workflow automation. without leaving the terminal.
ASK AI ABOUT THIS MCP SERVER
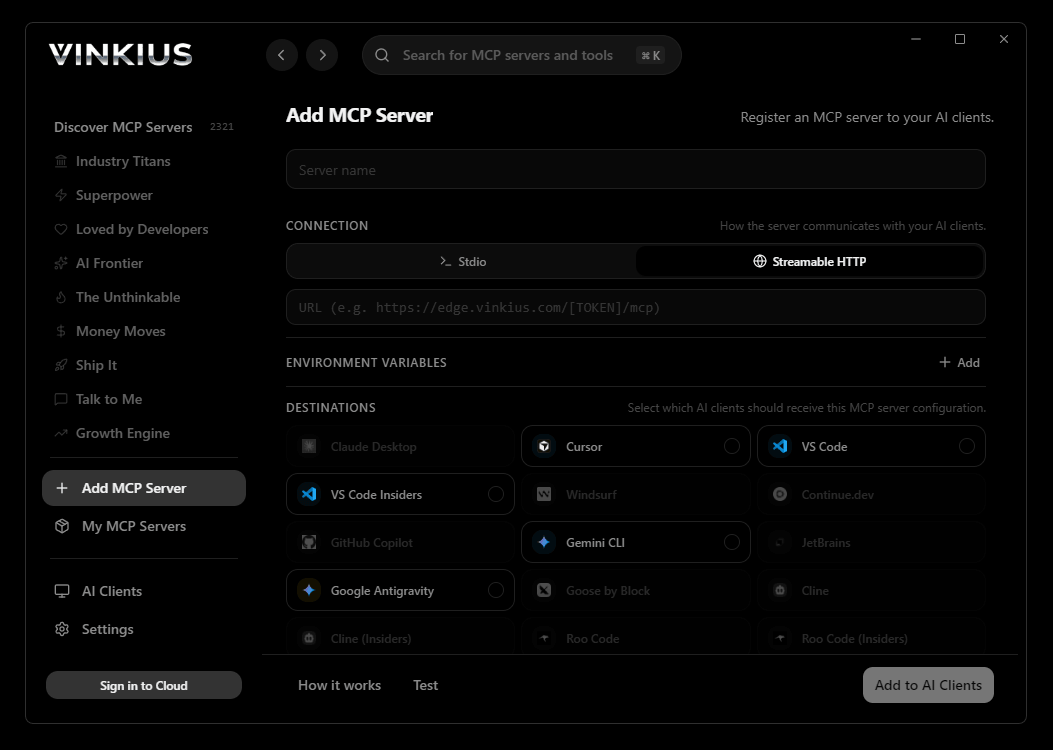
Vinkius supports streamable HTTP and SSE.
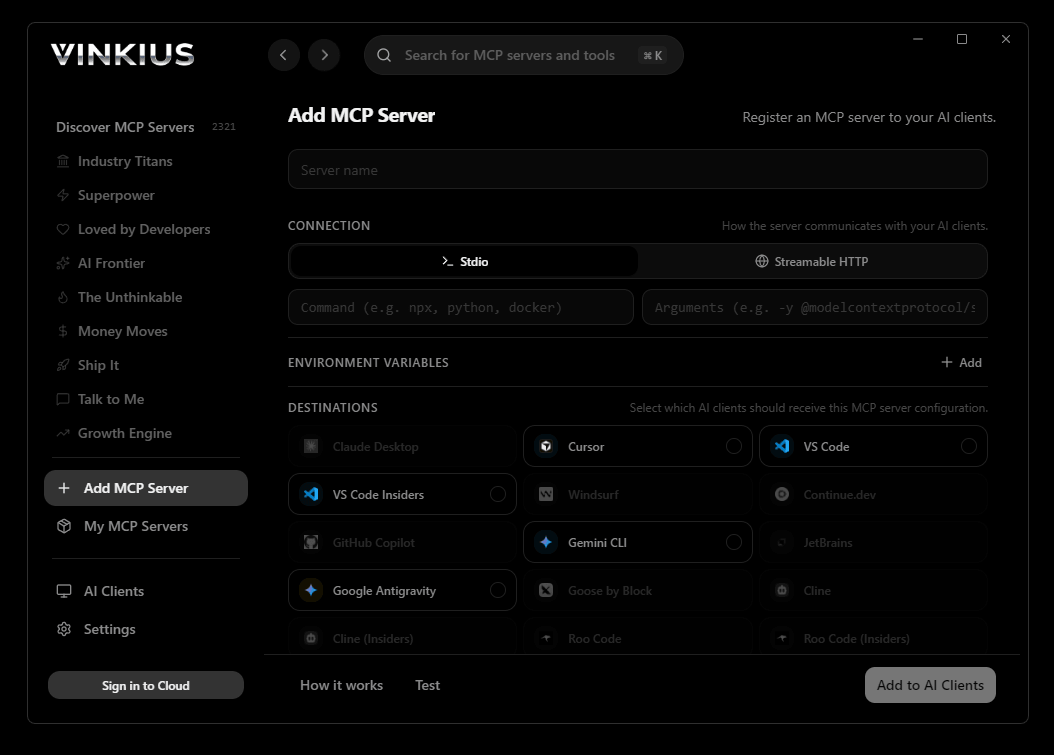
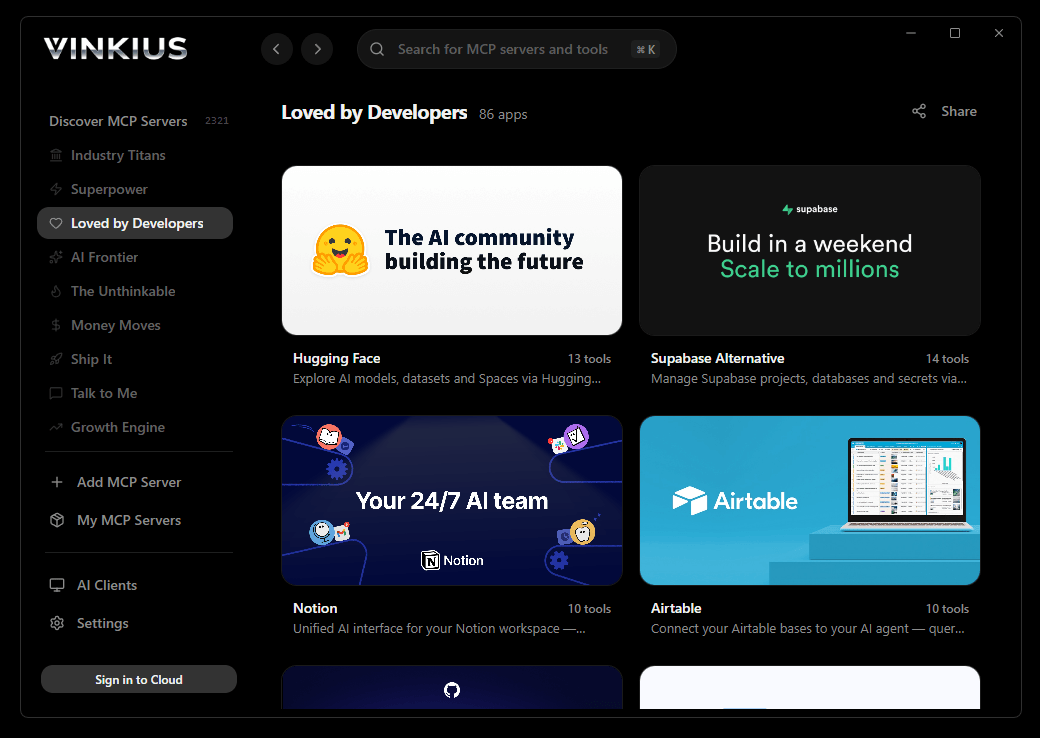
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Honeywell Forge and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"honeywell-forge": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Honeywell Forge MCP Server
Connect Honeywell Forge to any AI agent via MCP.
How to Connect Honeywell Forge to Cline via MCP
Follow these steps to integrate the Honeywell Forge MCP Server with Cline.
Open Cline MCP Settings
Click the MCP Servers icon in the Cline sidebar panel
Add remote server
Click "Add MCP Server" and paste the configuration above
Enable the server
Toggle the server switch to ON
Start using Honeywell Forge
Ask Cline: "Using Honeywell Forge, help me...". 11 tools available
Why Use Cline with the Honeywell Forge MCP Server
Cline provides unique advantages when paired with Honeywell Forge through the Model Context Protocol.
Cline operates autonomously. it reads your codebase, plans a strategy, and executes multi-step tasks including MCP tool calls without step-by-step prompts
Runs inside VS Code, so you get MCP tool access alongside your existing extensions, terminal, and version control in a single window
Cline can create, edit, and delete files based on MCP tool responses, enabling end-to-end automation from data retrieval to code generation
Transparent execution: every tool call and file change is shown in Cline's activity log for full visibility and approval before committing
Honeywell Forge + Cline Use Cases
Practical scenarios where Cline combined with the Honeywell Forge MCP Server delivers measurable value.
Autonomous feature building: tell Cline to fetch data from Honeywell Forge and scaffold a complete module with types, handlers, and tests
Codebase refactoring: use Honeywell Forge tools to validate live data while Cline restructures your code to match updated schemas
Automated testing: Cline fetches real responses from Honeywell Forge and generates snapshot tests or mocks based on actual payloads
Incident response: query Honeywell Forge for real-time status and let Cline generate hotfix patches based on the findings
Honeywell Forge MCP Tools for Cline (11)
These 11 tools become available when you connect Honeywell Forge to Cline via MCP:
acknowledge_alarm
Acknowledgment does not resolve or clear the underlying condition—it simply records that a human has reviewed the alarm and is aware of it. This updates the alarm state from "unacknowledged" to "acknowledged" in the Forge audit log, which is important for compliance and incident-tracking workflows. Provide the exact alarm ID as returned by get_alarms. Use this during incident response to track which alarms have been seen by the operations team. Acknowledge an active alarm in Honeywell Forge
get_alarms
Alarms cover a wide range of conditions: security breaches (door forced, tailgating), fire and life safety (smoke detector activation, pull station), HVAC faults, and system health warnings. Each alarm record includes severity level, timestamp, source device, description, and acknowledgment status. Optionally filter by building_id to scope results to a single site. Use this to triage active incidents, audit historical events, or identify recurring fault patterns. List active and historical alarms across all buildings or a specific building
get_building_details
Returns comprehensive metadata including HVAC zones, floor plans, linked subsystems (access control, fire life safety, video surveillance), energy targets, and operating schedules. Use this when you need a deep-dive view of a single site before performing operations like checking alarms or querying energy usage. Get detailed information about a specific Honeywell Forge building
get_door_status
The response includes whether the door is currently open or closed, locked or unlocked, and any active fault conditions such as "door held open" or "forced open". This is a read-only, point-in-time snapshot—use it to verify the physical state of a door before granting access or investigating a security event. Get the real-time status of a specific door or access point
get_energy_usage
Returns aggregated consumption data including total kWh, cost estimates, demand peaks, and breakdowns by subsystem (HVAC, lighting, plug loads). Metrics may be presented as time-series data points with timestamps, allowing trend analysis and comparison against energy budgets. Use this to monitor sustainability KPIs, identify wasteful consumption patterns, or prepare energy audit reports for facility managers. Get energy consumption data for a specific building
get_temperature_data
Returns data points including zone temperature, setpoint targets, humidity levels, and HVAC equipment status (compressor running, valve position, fan speed). This data is essential for thermal comfort analysis, energy optimization, and proactive maintenance—such as identifying zones that consistently deviate from setpoints or detecting equipment degradation before failure. Use this to diagnose comfort complaints or validate HVAC scheduling changes. Get temperature and HVAC sensor data for a specific building
list_access_points
An access point represents a physical entry device—door, gate, turnstile, or barrier—managed by the Forge access control subsystem. Each record includes the access point ID, name, current lock state, door status (open/closed/forced), assigned access level, and the zone it belongs to. Use this to audit physical security surfaces before running lock/unlock commands or investigating door-forced alarm events. List all access control points (doors, gates, turnstiles) for a building
list_buildings
Each record contains the building identifier, name, address, operational status, and metadata such as time zone and total floor area. Use this tool as the entry point for any building-centric workflow—once you have the building ID you can drill down into access points, alarms, energy metrics, or video feeds. List all buildings registered in Honeywell Forge
list_video_feeds
Each record represents a camera or NVR channel with metadata including camera name, location within the building, stream URL (RTSP or HLS), resolution, current online/offline status, and recording mode (continuous, motion-triggered, scheduled). Use this to discover which cameras are available for live viewing or forensic review, and to map camera IDs to physical locations before correlating video with alarm events. List available video surveillance feeds for a building
lock_door
The door will immediately engage its locking mechanism and transition to a secured state. Only authorized credentials holders can override this lock via normal badge or PIN access. Use this when securing a building after hours, during a lockdown event, or to enforce temporary access restrictions. Confirm the door identity with list_access_points before executing. Lock a specific door or access point in Honeywell Forge
unlock_door
The door will disengage its lock and enter a free-access state until explicitly re-locked or returned to its scheduled access control mode. Use this for emergency egress, visitor accommodation, or maintenance access. Always verify the correct access point ID before unlocking to avoid unintended security gaps. Unlock a specific door or access point in Honeywell Forge
Troubleshooting Honeywell Forge MCP Server with Cline
Common issues when connecting Honeywell Forge to Cline through the Vinkius, and how to resolve them.
Server shows error in sidebar
Honeywell Forge + Cline FAQ
Common questions about integrating Honeywell Forge MCP Server with Cline.
How does Cline connect to MCP servers?
Can Cline run MCP tools without approval?
Does Cline support multiple MCP servers at once?
Connect Honeywell Forge with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Honeywell Forge to Cline
Get your token, paste the configuration, and start using 11 tools in under 2 minutes. No API key management needed.
