Lacework (Cloud Security & CNAPP) MCP Server for Claude Desktop 10 tools — connect in under 2 minutes
Claude Desktop is Anthropic's native application for interacting with Claude AI models on macOS and Windows. It was the first consumer application to ship with built-in MCP support, making it the reference implementation for the Model Context Protocol standard.
ASK AI ABOUT THIS MCP SERVER
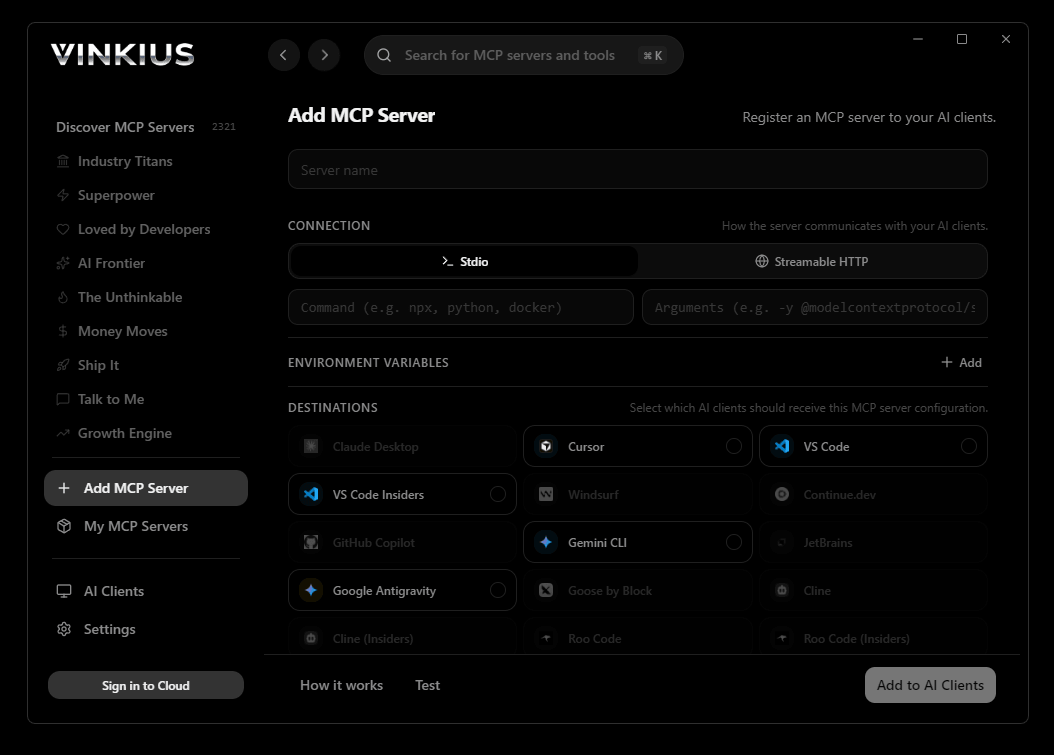
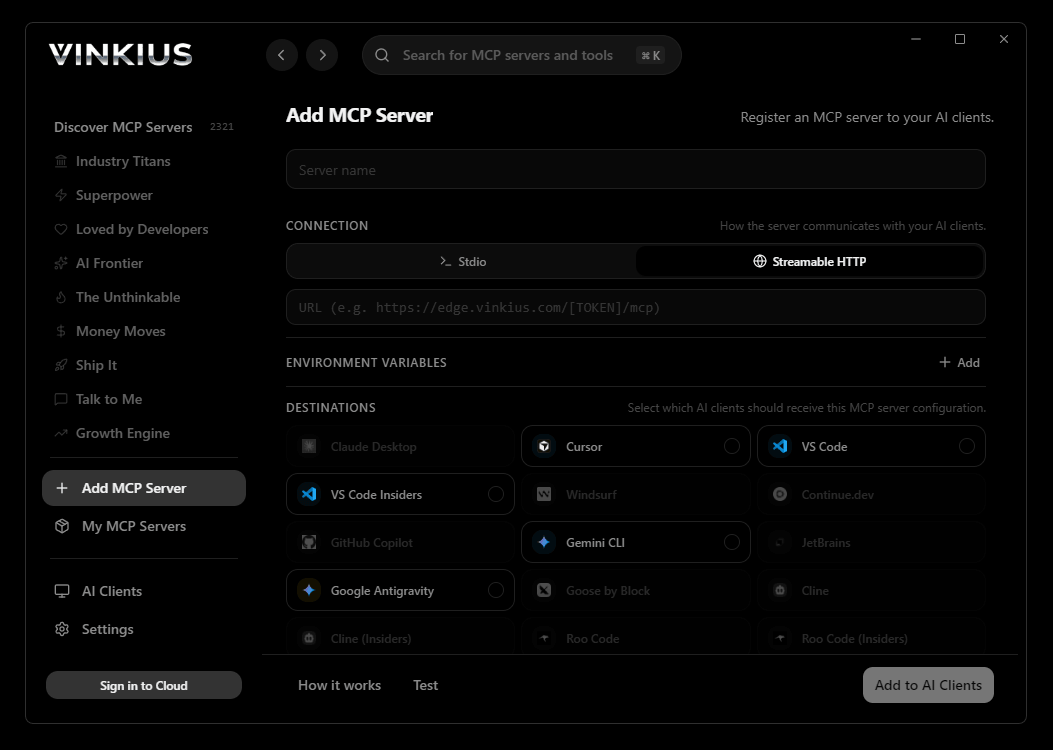
Vinkius supports streamable HTTP and SSE.
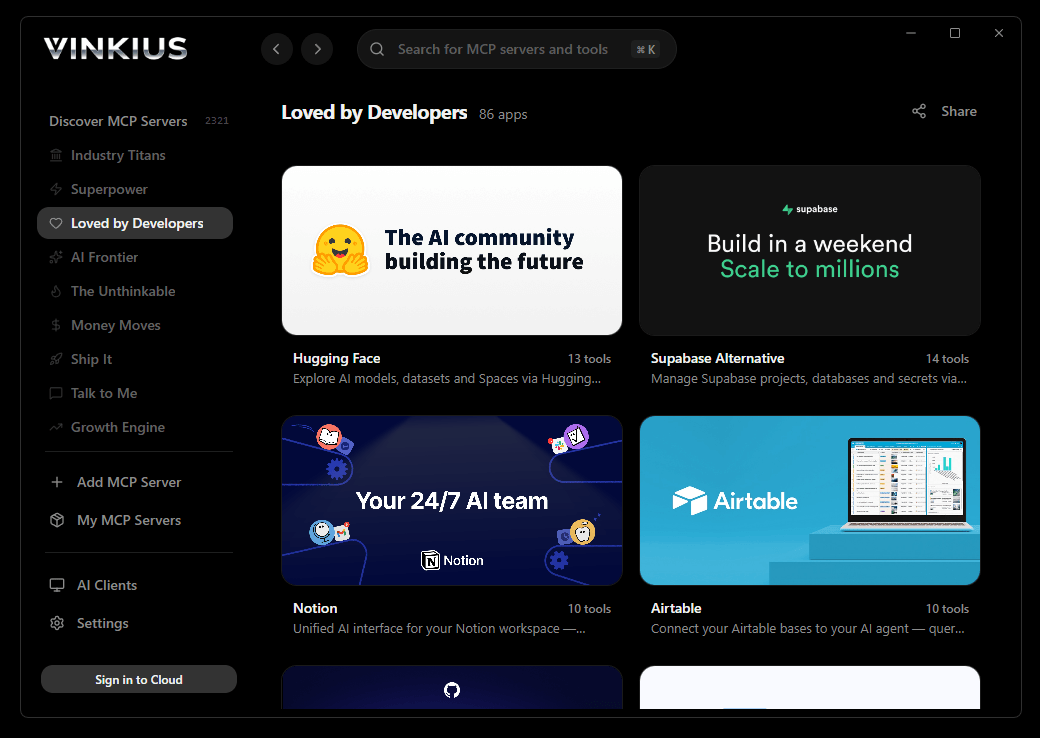
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Lacework (Cloud Security & CNAPP) and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"lacework-cloud-security-cnapp": {
// Your Vinkius token. get it at cloud.vinkius.com
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Lacework (Cloud Security & CNAPP) MCP Server
Connect your Lacework (FortiCNAPP) account to any AI agent and take full control of your cloud security posture and threat hunting through natural conversation.
Claude Desktop is the definitive way to connect Lacework (Cloud Security & CNAPP) to your AI workflow. Add Vinkius Edge URL to your config, restart the app, and Claude immediately exposes all 10 tools in the chat interface. ask a question, Claude calls the right tool, and you see the answer. Zero code, zero context switching.
What you can do
- Alert Orchestration — Search and retrieve deep behavioral telemetry for security alerts, identifying anomalous Kubernetes executions or AWS IAM brute-forcing attempts directly from your agent
- Vulnerability Management — List critical CVEs executing on cloud hosts and monitor static image vulnerabilities in your container registries (ECR, DockerHub)
- Emergency Incident Response — Instantly search your entire infrastructure for specific CVE exposure (e.g., Log4j) to identify vulnerable nodes during zero-day events
- Asset Inventory Audit — Query the real-time cloud control-plane to enumerate running instances, unrestricted S3 buckets, and active networking perimeters
- Threat Hunting (LQL) — Execute specialized Lacework Query Language (LQL) requests to analyze vast datasets for anomalous login patterns or API key abuse
- Compliance Monitoring — List and audit global cloud security policies to ensure your infrastructure remains within regulatory and organizational norms
The Lacework (Cloud Security & CNAPP) MCP Server exposes 10 tools through the Vinkius. Connect it to Claude Desktop in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Lacework (Cloud Security & CNAPP) to Claude Desktop via MCP
Follow these steps to integrate the Lacework (Cloud Security & CNAPP) MCP Server with Claude Desktop.
Open Claude Desktop Settings
Go to Settings → Developer → Edit Config to open claude_desktop_config.json
Add the MCP Server
Paste the configuration above into the mcpServers section
Restart Claude Desktop
Close and reopen Claude Desktop to load the new server
Start using Lacework (Cloud Security & CNAPP)
Look for the 🔌 icon in the chat. your 10 tools are now available
Why Use Claude Desktop with the Lacework (Cloud Security & CNAPP) MCP Server
Claude Desktop by Anthropic provides unique advantages when paired with Lacework (Cloud Security & CNAPP) through the Model Context Protocol.
Claude Desktop is the reference MCP client. it was designed alongside the protocol itself, ensuring the most complete and stable MCP implementation available
Zero-code configuration: add a server URL to a JSON file and Claude instantly discovers and exposes all available tools in the chat interface
Claude's extended thinking capability lets it reason through multi-step tool usage, chaining multiple API calls to answer complex questions
Enterprise-grade security with local config storage. your tokens never leave your machine, and connections go directly to Vinkius Edge network
Lacework (Cloud Security & CNAPP) + Claude Desktop Use Cases
Practical scenarios where Claude Desktop combined with the Lacework (Cloud Security & CNAPP) MCP Server delivers measurable value.
Interactive data exploration: ask Claude to query DNS records, look up WHOIS data, and cross-reference results in a single conversation
Ad-hoc security audits: type a domain name and let Claude enumerate subdomains, check DNS history, and flag configuration anomalies. all through natural language
Executive briefings: generate comprehensive domain intelligence reports by asking Claude to compile findings into a formatted summary
Learning and training: new team members can explore API capabilities conversationally without needing to read documentation
Lacework (Cloud Security & CNAPP) MCP Tools for Claude Desktop (10)
These 10 tools become available when you connect Lacework (Cloud Security & CNAPP) to Claude Desktop via MCP:
execute_query
Produces bespoke output matrices tracking API keys bypassing IAM logic, anomalous login patterns, or Kubernetes process spawn trees. Execute an LQL Threat Hunting Query on-demand
get_alert
Extracts precisely what baseline behavior was deviated from, providing deep contextual metadata such as explicit AWS Accounts involved, offending Container Image SHAs, and correlated external IP anomalies. Get exact behavioral payloads and telemetry for an Alert
list_container_vulnerabilities
Examines ECR/DockerHub registries or direct cluster deployments for images carrying critical inherited CVEs at the filesystem level before CI/CD promotion blocks. List static image vulnerabilities detected in Container Registries
list_host_vulnerabilities
Identifies running processes strictly matched against Critical or High CVEs (e.g., Log4j, Polkit) directly active inside EC2 or GCE instances. List known vulnerabilities executing natively on Cloud Hosts/VMs
list_lql_queries
These extract precise cloud telemetry fields mapping user-defined compliance checks directly against the underlying dataset. List all Lacework Query Language (LQL) structures
list_resource_groups
Helps define what constitutes "Production" vs "Staging" in Policy evaluation engines. List logical Resource Groups managing Lacework architectures
list_security_policies
Confirms whether Lacework will alert directly if an engineer violates structural norms (e.g., exposing port 22 directly to 0.0.0.0/0). List all global Cloud Security Policies enforced by Lacework
search_alerts
Fetches events mapping to anomalous Kubernetes executions, AWS IAM brute-forcing attempts, and massive container network exfiltrations spanning the specified time filter. Search Cloud Security alerts dynamically across Lacework
search_cloud_inventory
Used to dynamically enumerate running instances, active networking perimeters, or unrestricted S3 buckets discovered by cross-account role polling. Query the real-time Lacework Cloud Control-Plane Asset Inventory
search_cve_exposure
Directly filters the entire cloud infrastructure footprint determining exactly which specific nodes (Machines) are currently vulnerable to the designated CVE (e.g. "CVE-2026-0001"). Search all integrated Machines/Instances for a specific CVE
Example Prompts for Lacework (Cloud Security & CNAPP) in Claude Desktop
Ready-to-use prompts you can give your Claude Desktop agent to start working with Lacework (Cloud Security & CNAPP) immediately.
"Search for all Critical alerts from the last 24 hours"
"List all host vulnerabilities for our Production resource group"
"Are there any unrestricted S3 buckets currently visible in our inventory?"
Troubleshooting Lacework (Cloud Security & CNAPP) MCP Server with Claude Desktop
Common issues when connecting Lacework (Cloud Security & CNAPP) to Claude Desktop through the Vinkius, and how to resolve them.
Server not appearing after restart
~/Library/Application Support/Claude/claude_desktop_config.json (macOS) or %APPDATA%\\Claude\\ (Windows).Authentication error
Tools not showing in chat
Lacework (Cloud Security & CNAPP) + Claude Desktop FAQ
Common questions about integrating Lacework (Cloud Security & CNAPP) MCP Server with Claude Desktop.
How does Claude Desktop discover MCP tools?
claude_desktop_config.json file and connects to each configured MCP server. It calls the tools/list endpoint to fetch the schema for every available tool, then surfaces them as clickable options in the chat interface via the 🔌 icon.What happens if the MCP server is temporarily unavailable?
Can I connect multiple MCP servers simultaneously?
mcpServers section of the config file. Each server appears as a separate tool provider, and Claude can use tools from multiple servers in a single conversation turn.Is there a limit on the number of tools per server?
Does Claude Desktop support Streamable HTTP transport?
Connect Lacework (Cloud Security & CNAPP) with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Lacework (Cloud Security & CNAPP) to Claude Desktop
Get your token, paste the configuration, and start using 10 tools in under 2 minutes. No API key management needed.
