Patchstack Security MCP Server for VS Code Copilot 9 tools — connect in under 2 minutes
GitHub Copilot in VS Code is the most widely adopted AI coding assistant, embedded directly into the world's most popular code editor. With MCP support in Agent mode, Copilot can access external data and APIs to generate context-aware code grounded in real-time information.
ASK AI ABOUT THIS MCP SERVER
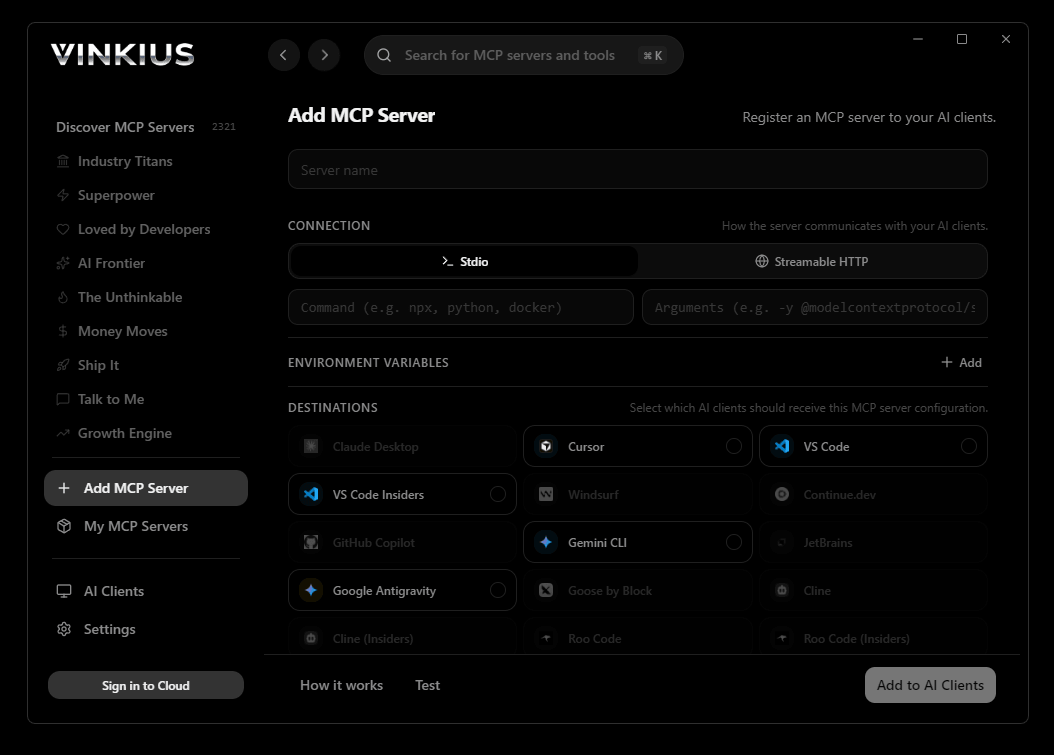
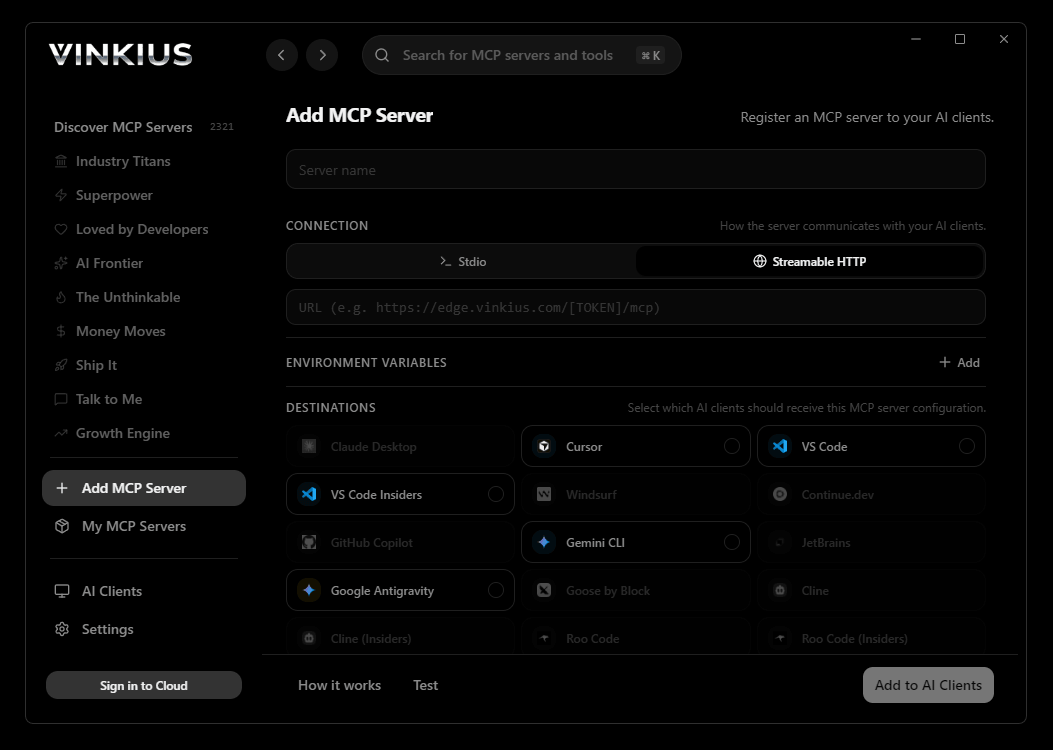
Vinkius supports streamable HTTP and SSE.
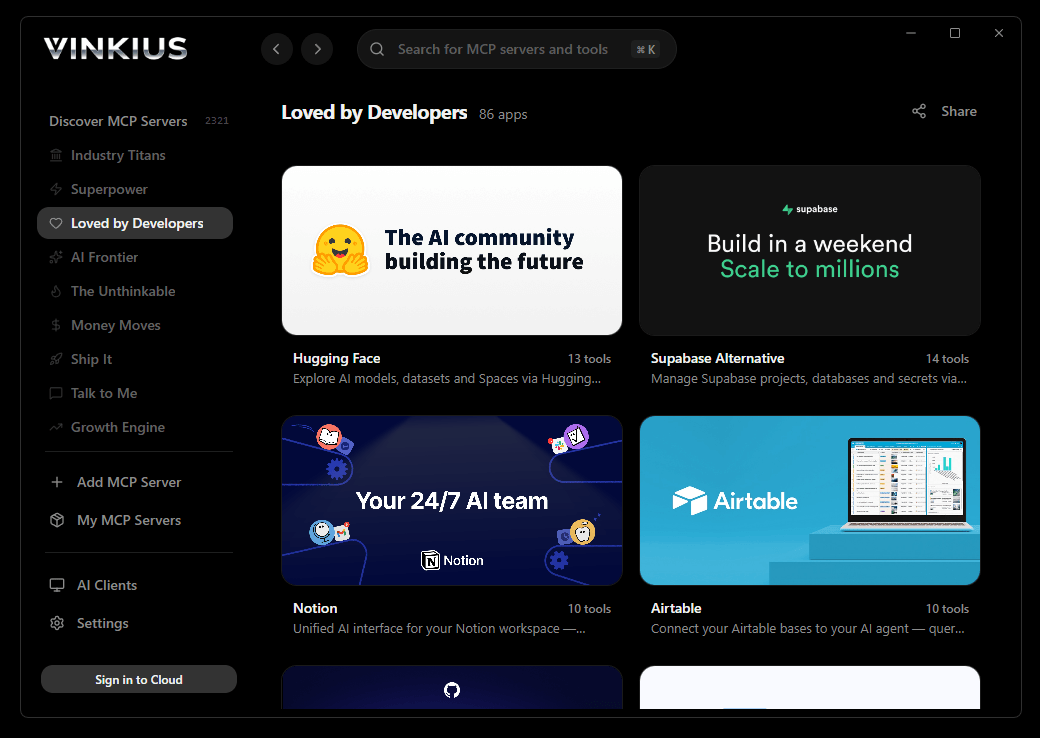
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Patchstack Security and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"patchstack-security": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Patchstack Security MCP Server
Connect your AI agent to Patchstack, the leading security platform for WordPress and PHP applications. This integration allows you to oversee the security status of all your monitored sites, track known vulnerabilities in plugins and themes, and audit security alerts through natural conversation.
GitHub Copilot Agent mode brings Patchstack Security data directly into your VS Code workflow. With a project-scoped config, the entire team shares access to 9 tools. Copilot queries live data, generates typed code, and writes tests from actual API responses, all without leaving the editor.
What you can do
- Software Oversight — Get a comprehensive overview of all plugins, themes, and core versions across your monitored sites
- Threat Intelligence — Search the massive Patchstack database for known vulnerabilities in specific WordPress components
- Live Alerts — Retrieve the latest security alerts and triggered firewall rules to stay ahead of attacks
- Site Auditing — List and inspect individual sites to check their security scores and vulnerability counts
- Auto-Update Management — Review your settings for automatic security patching of vulnerable components
The Patchstack Security MCP Server exposes 9 tools through the Vinkius. Connect it to VS Code Copilot in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Patchstack Security to VS Code Copilot via MCP
Follow these steps to integrate the Patchstack Security MCP Server with VS Code Copilot.
Create MCP config
Create a .vscode/mcp.json file in your project root
Add the server config
Paste the JSON configuration above
Enable Agent mode
Open GitHub Copilot Chat and switch to Agent mode using the dropdown
Start using Patchstack Security
Ask Copilot: "Using Patchstack Security, help me...". 9 tools available
Why Use VS Code Copilot with the Patchstack Security MCP Server
GitHub Copilot for Visual Studio Code provides unique advantages when paired with Patchstack Security through the Model Context Protocol.
VS Code is used by over 70% of developers. adding MCP tools to Copilot means your team can leverage external data without leaving their primary editor
Project-scoped MCP configs (`.vscode/mcp.json`) let you commit server configurations to your repository, ensuring the entire team shares the same tool access
Copilot's Agent mode integrates MCP tools seamlessly with file editing, terminal commands, and workspace search in a single agentic loop
GitHub's enterprise compliance and audit features extend to MCP tool usage, providing visibility into how AI interacts with external services
Patchstack Security + VS Code Copilot Use Cases
Practical scenarios where VS Code Copilot combined with the Patchstack Security MCP Server delivers measurable value.
Live API integration: Copilot can query an MCP server, inspect the response schema, and generate typed API client code in the same step
DevSecOps workflows: security teams can give developers access to domain intelligence tools directly in their editor for real-time vulnerability assessment during code review
Data pipeline development: Copilot fetches sample data via MCP and generates transformation scripts, validators, and test fixtures from actual API responses
Documentation generation: Copilot queries available tools and auto-generates README sections, API reference docs, and usage examples
Patchstack Security MCP Tools for VS Code Copilot (9)
These 9 tools become available when you connect Patchstack Security to VS Code Copilot via MCP:
get_autoupdate_settings
Retrieve settings for automatic updates of vulnerable components
get_component_vulnerabilities
Retrieve all known vulnerabilities for a specific component
get_latest_alerts
Retrieve the latest security alerts and triggered rules
get_latest_vulnerabilities
Retrieve the latest vulnerabilities added to the database
get_site_software
Retrieve a list of all software installed on a specific site
get_software_overview
Retrieve a security overview of all software across your sites
get_vulnerability_details
Get detailed information for a specific vulnerability
list_sites
Retrieve a list of all sites monitored by Patchstack
search_vulnerabilities
Search the Patchstack vulnerability database
Example Prompts for Patchstack Security in VS Code Copilot
Ready-to-use prompts you can give your VS Code Copilot agent to start working with Patchstack Security immediately.
"List all my monitored sites in Patchstack."
"Search for vulnerabilities in the 'Contact Form 7' plugin."
Troubleshooting Patchstack Security MCP Server with VS Code Copilot
Common issues when connecting Patchstack Security to VS Code Copilot through the Vinkius, and how to resolve them.
MCP tools not available
Patchstack Security + VS Code Copilot FAQ
Common questions about integrating Patchstack Security MCP Server with VS Code Copilot.
Which VS Code version supports MCP?
How do I switch to Agent mode?
Can I restrict which MCP tools Copilot can access?
Does MCP work in VS Code Remote or Codespaces?
.vscode/mcp.json work in Remote SSH, WSL, and GitHub Codespaces environments. The MCP connection is established from the remote host, so ensure the server URL is accessible from that environment.Connect Patchstack Security with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Patchstack Security to VS Code Copilot
Get your token, paste the configuration, and start using 9 tools in under 2 minutes. No API key management needed.
