Patchstack Security MCP Server for Windsurf 9 tools — connect in under 2 minutes
Windsurf brings agentic AI coding to a purpose-built IDE. Connect Patchstack Security through Vinkius and Cascade will auto-discover every tool. ask questions, generate code, and act on live data without leaving your editor.
ASK AI ABOUT THIS MCP SERVER
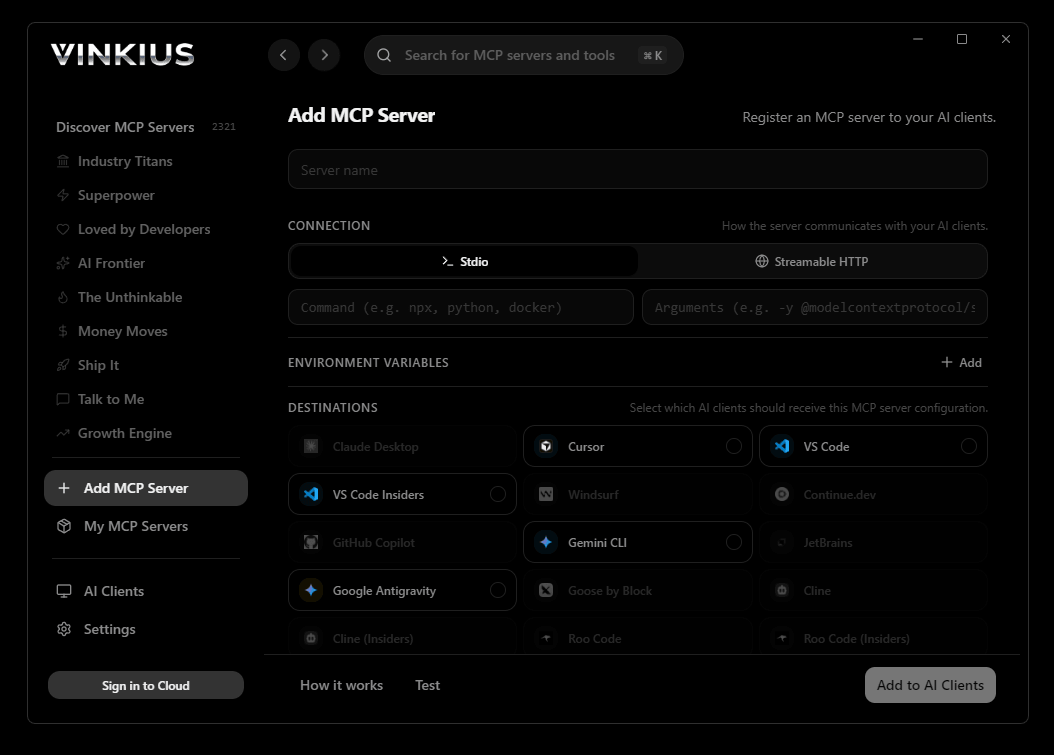
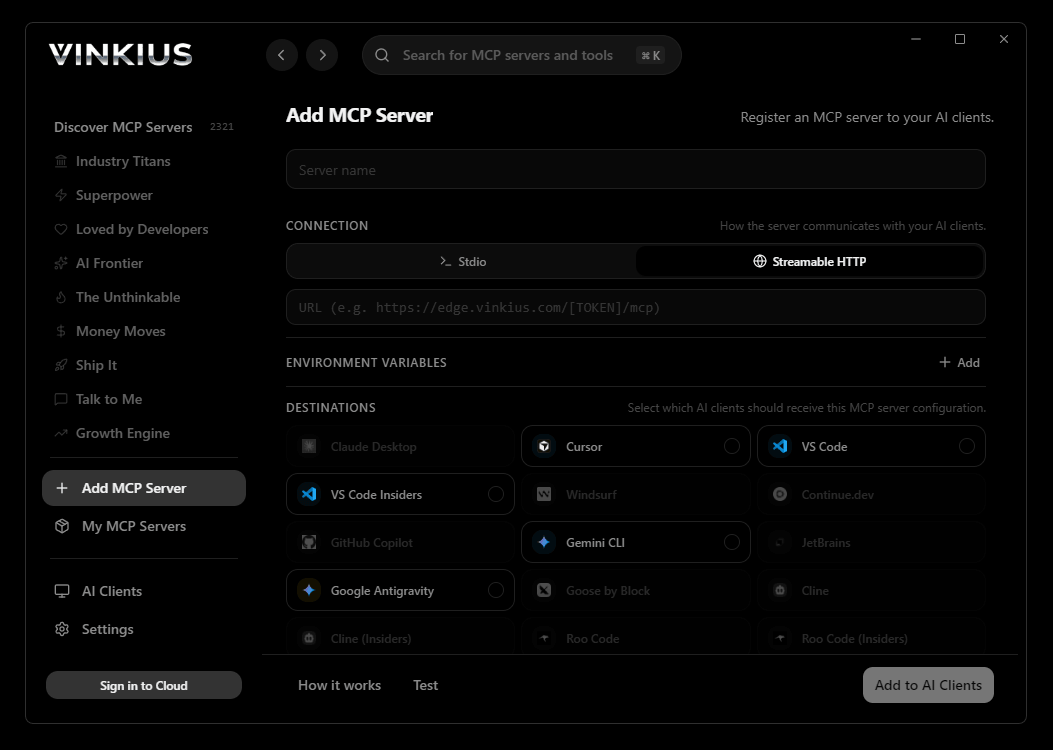
Vinkius supports streamable HTTP and SSE.
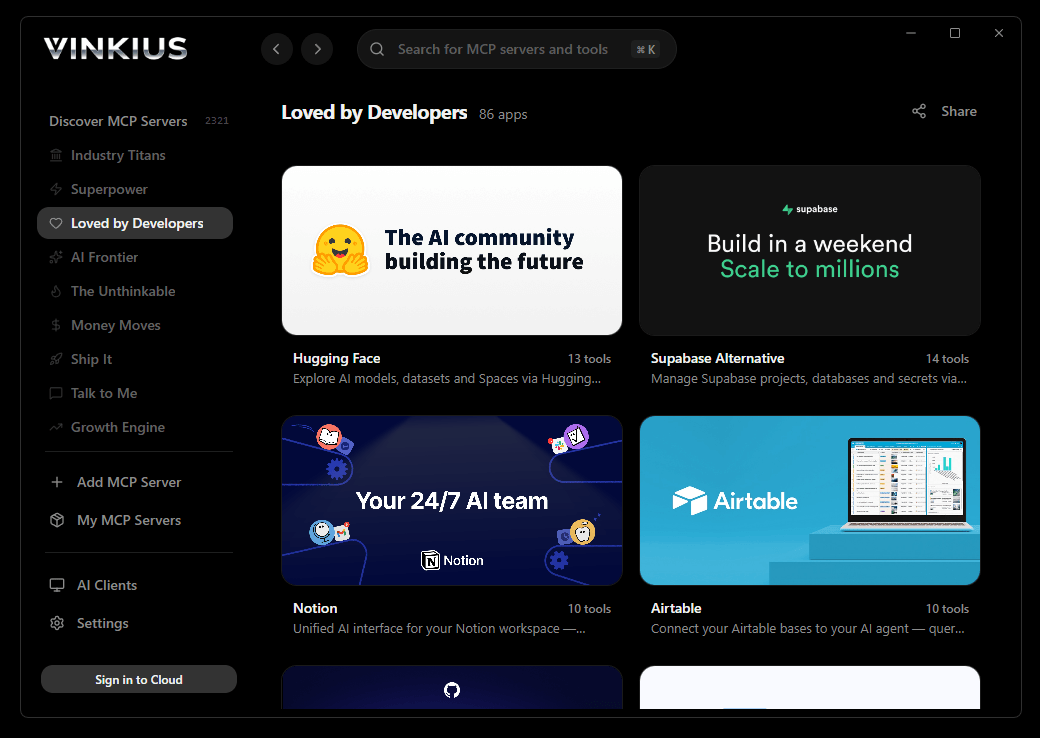
Vinkius Desktop App
The modern way to manage MCP Servers — no config files, no terminal commands. Install Patchstack Security and 2,500+ MCP Servers from a single visual interface.

{
"mcpServers": {
"patchstack-security": {
"url": "https://edge.vinkius.com/[YOUR_TOKEN_HERE]/mcp"
}
}
}
* Every MCP server runs on Vinkius-managed infrastructure inside AWS - a purpose-built runtime with per-request V8 isolates, Ed25519 signed audit chains, and sub-40ms cold starts optimized for native MCP execution. See our infrastructure
About Patchstack Security MCP Server
Connect your AI agent to Patchstack, the leading security platform for WordPress and PHP applications. This integration allows you to oversee the security status of all your monitored sites, track known vulnerabilities in plugins and themes, and audit security alerts through natural conversation.
Windsurf's Cascade agent chains multiple Patchstack Security tool calls autonomously. query data, analyze results, and generate code in a single agentic session. Paste Vinkius Edge URL, reload, and all 9 tools are immediately available. Real-time tool feedback appears inline, so you see API responses directly in your editor.
What you can do
- Software Oversight — Get a comprehensive overview of all plugins, themes, and core versions across your monitored sites
- Threat Intelligence — Search the massive Patchstack database for known vulnerabilities in specific WordPress components
- Live Alerts — Retrieve the latest security alerts and triggered firewall rules to stay ahead of attacks
- Site Auditing — List and inspect individual sites to check their security scores and vulnerability counts
- Auto-Update Management — Review your settings for automatic security patching of vulnerable components
The Patchstack Security MCP Server exposes 9 tools through the Vinkius. Connect it to Windsurf in under two minutes — no API keys to rotate, no infrastructure to provision, no vendor lock-in. Your configuration, your data, your control.
How to Connect Patchstack Security to Windsurf via MCP
Follow these steps to integrate the Patchstack Security MCP Server with Windsurf.
Open MCP Settings
Go to Settings → MCP Configuration or press Cmd+Shift+P and search "MCP"
Add the server
Paste the JSON configuration above into mcp_config.json
Save and reload
Windsurf will detect the new server automatically
Start using Patchstack Security
Open Cascade and ask: "Using Patchstack Security, help me...". 9 tools available
Why Use Windsurf with the Patchstack Security MCP Server
Windsurf provides unique advantages when paired with Patchstack Security through the Model Context Protocol.
Windsurf's Cascade agent autonomously chains multiple tool calls in sequence, solving complex multi-step tasks without manual intervention
Purpose-built for agentic workflows. Cascade understands context across your entire codebase and integrates MCP tools natively
JSON-based configuration means zero code changes: paste a URL, reload, and all 9 tools are immediately available
Real-time tool feedback is displayed inline, so you see API responses directly in your editor without switching contexts
Patchstack Security + Windsurf Use Cases
Practical scenarios where Windsurf combined with the Patchstack Security MCP Server delivers measurable value.
Automated code generation: ask Cascade to fetch data from Patchstack Security and generate models, types, or handlers based on real API responses
Live debugging: query Patchstack Security tools mid-session to inspect production data while debugging without leaving the editor
Documentation generation: pull schema information from Patchstack Security and have Cascade generate comprehensive API docs automatically
Rapid prototyping: combine Patchstack Security data with Cascade's code generation to scaffold entire features in minutes
Patchstack Security MCP Tools for Windsurf (9)
These 9 tools become available when you connect Patchstack Security to Windsurf via MCP:
get_autoupdate_settings
Retrieve settings for automatic updates of vulnerable components
get_component_vulnerabilities
Retrieve all known vulnerabilities for a specific component
get_latest_alerts
Retrieve the latest security alerts and triggered rules
get_latest_vulnerabilities
Retrieve the latest vulnerabilities added to the database
get_site_software
Retrieve a list of all software installed on a specific site
get_software_overview
Retrieve a security overview of all software across your sites
get_vulnerability_details
Get detailed information for a specific vulnerability
list_sites
Retrieve a list of all sites monitored by Patchstack
search_vulnerabilities
Search the Patchstack vulnerability database
Example Prompts for Patchstack Security in Windsurf
Ready-to-use prompts you can give your Windsurf agent to start working with Patchstack Security immediately.
"List all my monitored sites in Patchstack."
"Search for vulnerabilities in the 'Contact Form 7' plugin."
Troubleshooting Patchstack Security MCP Server with Windsurf
Common issues when connecting Patchstack Security to Windsurf through the Vinkius, and how to resolve them.
Server not connecting
Patchstack Security + Windsurf FAQ
Common questions about integrating Patchstack Security MCP Server with Windsurf.
How does Windsurf discover MCP tools?
mcp_config.json file on startup and connects to each configured server via Streamable HTTP. Tools are listed in the MCP panel and available to Cascade automatically.Can Cascade chain multiple MCP tool calls?
Does Windsurf support multiple MCP servers?
mcp_config.json. Each server's tools appear in the MCP panel and Cascade can use tools from different servers in a single flow.Connect Patchstack Security with your favorite client
Step-by-step setup guides for every MCP-compatible client and framework:
Anthropic's native desktop app for Claude with built-in MCP support.
AI-first code editor with integrated LLM-powered coding assistance.
GitHub Copilot in VS Code with Agent mode and MCP support.
Purpose-built IDE for agentic AI coding workflows.
Autonomous AI coding agent that runs inside VS Code.
Anthropic's agentic CLI for terminal-first development.
Python SDK for building production-grade OpenAI agent workflows.
Google's framework for building production AI agents.
Type-safe agent development for Python with first-class MCP support.
TypeScript toolkit for building AI-powered web applications.
TypeScript-native agent framework for modern web stacks.
Python framework for orchestrating collaborative AI agent crews.
Leading Python framework for composable LLM applications.
Data-aware AI agent framework for structured and unstructured sources.
Microsoft's framework for multi-agent collaborative conversations.
Connect Patchstack Security to Windsurf
Get your token, paste the configuration, and start using 9 tools in under 2 minutes. No API key management needed.
