Fort Knox
The best Fort Knox connectors for your AI agents.

CrowdStrike Falcon
8 toolsDetect threats, manage endpoints, investigate incidents, and query telemetry from CrowdStrike Falcon — the #1 endpoint detection and response platform.

Plaid Enterprise Banking
10 toolsUltimate Open Banking: balances, transactions, ML fraud logic, payroll, and asset verification.

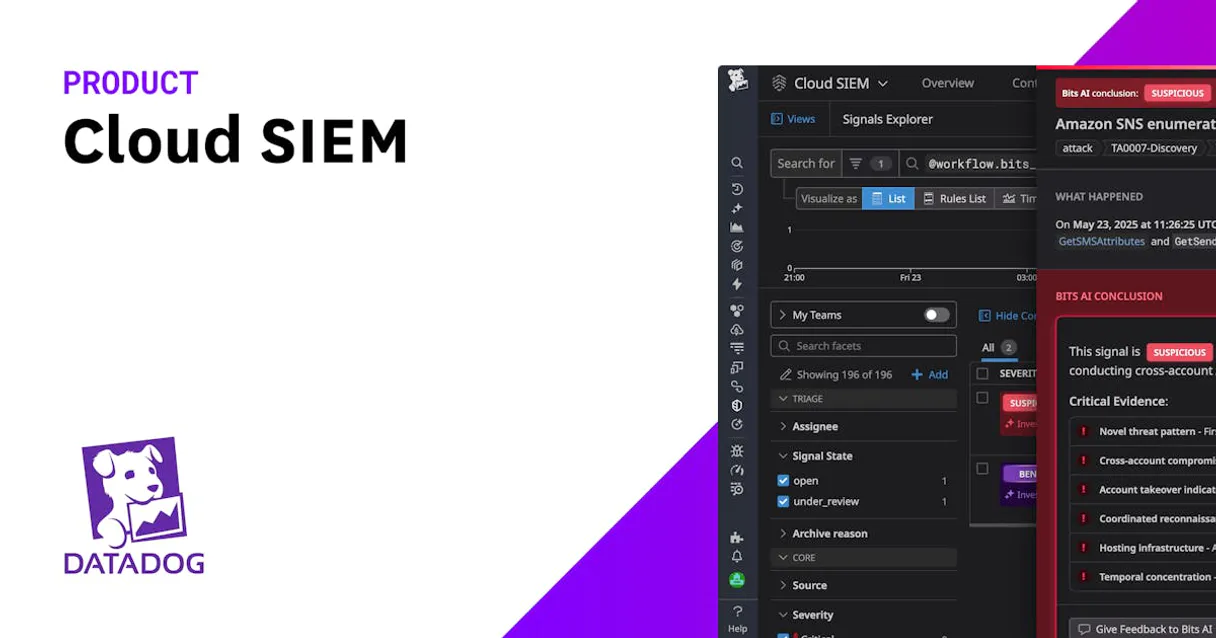
Datadog Cloud SIEM
10 toolsManage cloud security via Datadog — search security signals, triage alerts, and audit detection rules directly from any AI agent.

Okta
10 toolsEquip your AI agent with Okta Identity Cloud to manage users, groups, and seamless authentication effortlessly.

Amazon S3
10 toolsCloud object storage orchestration — manage buckets, objects, and metadata via AI.
Auth0
10 toolsManage IAM operations—users, clients, connections, and logs in your Auth0 tenant directly via your AI agent.
Brex
10 toolsEquip your AI to navigate your Brex suite. Spin up virtual cards, route new team members, and check daily cash allocations through natural chat.

Checkmarx
10 toolsAutomate AppSec via Checkmarx One — trigger core scans, analyze vulnerabilities, discover Best Fix Locations (BFL), and monitor KICS results.

Clerk
8 toolsManage authentication and users via Clerk — track active sessions, monitor organizations, and manage invitations directly from any AI agent.

CyberArk Privilege Cloud
10 toolsManage privileged access via CyberArk — audit secure safes, checkout vaulted account passwords, monitor users, and terminate sessions directly from any AI agent.

Snyk
9 toolsBring your Snyk code security ecosystem directly to your AI. Analyze vulnerabilities, project metadata, and scan issues right from your editor.

Auth0 Alternative
13 toolsManage identity and access via Auth0 — list users, create accounts, audit logs, manage clients and review connections from any AI agent.

Doppler
12 toolsManage secrets and environment variables via Doppler — list projects, audit secrets, and track activity logs from any AI agent.
Black Duck (Synopsys)
10 toolsSecure your open source supply chain via Black Duck — list projects, versions, and vulnerabilities directly from any AI agent.

BugSnag
10 toolsMonitor application errors via BugSnag — track stability, inspect error groups, and retrieve event details directly from any AI agent.
CockroachDB Cloud
8 toolsManage distributed SQL clusters via CockroachDB Cloud — track clusters, monitor nodes, and audit network allowlists directly from any AI agent.

Elastic Security
10 toolsManage SIEM and SOC operations via Elastic Security — monitor detection rules, search security alerts (Signals), handle whitelisting, and audit threat coverage directly from any AI agent.

Google Cloud Storage
12 toolsManage your GCS buckets and objects — list files, upload data, and audit permissions via AI.

Jamf Pro
10 toolsManage Apple devices, computers, and inventory via Jamf Pro API.

Lacework (Cloud Security & CNAPP)
10 toolsSecure your cloud via Lacework — search security alerts, monitor vulnerabilities, and audit cloud asset inventory.

NIST NVD
10 toolsAccess authoritative vulnerability and product data via NIST NVD — track CVEs, CPEs, and security history directly from your AI agent.

OneTrust
10 toolsManage privacy requests, assessments, vendors, consent, and incidents via OneTrust — automate GDPR, CCPA, and data governance from any AI agent.

Ping Identity
10 toolsManage PingOne user identities, applications, groups, risk policies, and sign-on flows autonomously via AI.

Semgrep
10 toolsEquip your AI agent with read/write access to Semgrep's SAST platform to audit code security findings, update triage statuses, and enforce custom semantic rules.

Tenable
10 toolsManage Tenable Vulnerability Management scans, inspect cloud assets, and triage CVEs natively via your AI agent.

Trend Micro
8 toolsEquip your AI agent with Vision One telemetry to investigate threats, audit endpoint activities, and manage security alerts natively.

Vanta
10 toolsManage your automated compliance and security posture. Audit users, devices, vendors, and vulnerabilities directly from your AI agent.
Have I Been Pwned
5 toolsCheck if your accounts or passwords have been compromised in data breaches using the HIBP service.

Aikido Security
16 toolsQuery security vulnerabilities via Aikido — list open issues, check repositories, monitor cloud assets, and track compliance directly from any AI agent.
HCL AppScan
10 toolsManage security scans and vulnerabilities with HCL AppScan — track issues and audit applications via AI.

Drata
10 toolsAutomate compliance and security via Drata — monitor controls, track personnel onboarding, audit policies, and verify cloud asset security directly from any AI agent.

HackerOne
10 toolsAutomate bug bounty management via HackerOne — manage reports, programs, and payments directly from any AI agent.

JumpCloud
10 toolsManage users, systems, and directories via JumpCloud API.

Nmap Online
10 toolsPerform network discovery and security auditing via Nmap — track port scans, DNS lookups, and traceroutes directly from your AI agent.

Rapid7 InsightVM
10 toolsEquip your AI to interact directly with Rapid7 InsightVM, extracting vulnerability assessments, scanning network assets, and launching immediate scans.

Salt Security
10 toolsIntegrate Salt Security directly with your AI for comprehensive API threat vector discovery, posture management, and active remediation in real-time.

Veracode
10 toolsBring Veracode AppSec to your AI. Analyze source code flaws, extract application profiles, and track vulnerabilities conversationaly.

WorkOS
10 toolsManage enterprise organizations, SSO connections, and directory sync on WorkOS — the platform for enterprise-ready features.

Censys
9 toolsSearch internet-connected hosts, SSL certificates and attack surface — discover exposed services and vulnerabilities.

Aporia
7 toolsMonitor AI models and validate LLM interactions with guardrails directly from your AI agent to ensure safety and observability.